-
How to avoid phishing fraud scam
Reposted from: https://lemmings.world/post/10865023
> 1. Recognize the common signs > > • Urgent or emotionally appealing language > • Requests to send personal or financial information > • Unexpected attachments > • Untrusted shortened URLs > • Email addresses that do not match the supposed sender > • Poor writing/misspellings (less common) > > 2. Resist and report > Report suspicious messages by using the “report spam” feature. > If the message is designed to resemble an organization you trust, report the message by alerting the organization using their contact information found on their webpage. > > I have found also these phishing reporting pages: > > SITE: https://safebrowsing.google.com/safebrowsing/report_phish/ > > SITE: https://www.ncsc.gov.uk/section/about-this-website/report-scam-website > > SITE: https://www.scamwatcher.com/scam/add?type=fraudulent_website > > SITE/EMAIL: https://report.netcraft.com/report ( scam [\AT\] netcraft [\D0T\] com - for a phishing/fraud mail forwarding ) > > EMAIL: https://www.ncsc.gov.uk/collection/phishing-scams/report-scam-email#section_1 - forward phish mail to report [\AT\] phishing [\D0T\] gov [\D0T\] uk > > EMAIL: https://apwg.org/reportphishing/ ( reportphishing [\AT\] apwg [\D0T\] org - forward phishing mail as attachment if possible ) > > EMAIL: phishing-report [\AT\] us-cert [\D0T\] gov (phishing message should be sent as attachment possibly or its full source code in a message BODY.) > > OTHER: https://www.knowbe4.com/free-phish-alert (email client extension) > > feedback or new additions are welcome > > 3. Delete > Delete the message. Don’t reply or click on any attachment or link, including any “unsubscribe” link. > The unsubscribe button could also carry a link used for phishing. Just delete > > _________________________________________________ > > Source: https://www.cisa.gov/secure-our-world/recognize-and-report-phishing > > Send this to your friends, especially internet beginners.
- www.tomshardware.com Firmware flaw affects numerous generations of Intel CPUs — UEFI code execution vulnerability found for Intel CPUs from 14th Gen Raptor Lake to 6th Gen Skylake CPUs, and TPM will not save you
Eclypsium Automata uncovers Phoenix as the latest to fall to a significant Arbitrary Code Execution exploit impacting Lenovo, AMI, Insyde, and Intel motherboard firmware.
-
BusKill Warrant Canary for 2024 H2 🕵️
www.buskill.in BusKill Canary #8 - BusKillThis post contains the cryptographically-signed BusKill warrant canary #008 for June 2024 to January 2025.

This post contains a canary message that's cryptographically signed by the official BusKill PGP release key
| [!BusKill Canary #008](https://www.buskill.in/canary-008/) | |:--:| | The BusKill project just published their Warrant Canary #008 |
For more information about BusKill canaries, see:
- <https://buskill.in/canary>
``` -----BEGIN PGP SIGNED MESSAGE----- Hash: SHA512
Status: All good Release: 2024-06-11 Period: 2024-06-01 to 2024-12-31 Expiry: 2025-01-31
Statements ==========
The BusKill Team who have digitally signed this file [1] state the following:
-
The date of issue of this canary is June 11, 2024.
-
The current BusKill Signing Key (2020.07) is
E0AF FF57 DC00 FBE0 5635 8761 4AE2 1E19 36CE 786A
-
We positively confirm, to the best of our knowledge, that the integrity of our systems are sound: all our infrastructure is in our control, we have not been compromised or suffered a data breach, we have not disclosed any private keys, we have not introduced any backdoors, and we have not been forced to modify our system to allow access or information leakage to a third party in any way.
-
We plan to publish the next of these canary statements before the Expiry date listed above. Special note should be taken if no new canary is published by that time or if the list of statements changes without plausible explanation.
Special announcements =====================
None.
Disclaimers and notes =====================
This canary scheme is not infallible. Although signing the declaration makes it very difficult for a third party to produce arbitrary declarations, it does not prevent them from using force or other means, like blackmail or compromising the signers' laptops, to coerce us to produce false declarations.
The news feeds quoted below (Proof of freshness) serves to demonstrate that this canary could not have been created prior to the date stated. It shows that a series of canaries was not created in advance.
This declaration is merely a best effort and is provided without any guarantee or warranty. It is not legally binding in any way to anybody. None of the signers should be ever held legally responsible for any of the statements made here.
Proof of freshness ==================
04 Jun 24 14:10:16 UTC
Source: DER SPIEGEL - International (https://www.spiegel.de/international/index.rss) Fortress Europe: Migrants Abandoned on the Edge of the Sahara Israel-Gaza-Krieg: Menschenrechtler Aryeh Neier über Schuldfrage und Strafverfolgung (Kopie)
Source: NYT > World News (https://rss.nytimes.com/services/xml/rss/nyt/World.xml) Middle East Crisis: Israeli Airstrikes Kill Iranian General in Syria Live Updates: India’s Election Results Suggest a Setback for Modi
Source: BBC News - World (https://feeds.bbci.co.uk/news/world/rss.xml) Shock for India's Modi as opposition set to slash majority Gaza ceasefire plan turns into deadly game of survival
Source: Bitcoin Blockchain (https://blockchain.info/q/latesthash) 000000000000000000014cd79802b29c1dcd7fc6debee1e3968cfc216b59bf16
-----BEGIN PGP SIGNATURE-----
iQIzBAEBCgAdFiEEeY3BEB897EKK3hJNaLi8sMUCOQUFAmZfIwgACgkQaLi8sMUC OQXZYA/9ElVoUy3Um3IXFSwUGO+ctkvKd6idD7RuOBjqZyfadr4emrDrfQKYbCpa Gik4M1H/GWobO/RaDjeSjQtGUmlPn8anhoFzmI6pPz7fBSfg5VGemllyHI2ypPpf cJ1jLrmzpDGxLqPd/R/WsoE8dY9E7q20JgNESAqEYyjmjxqOjx6EnIjBjy8u+xL3 YWBw5BQn/1XbLXw4X7WJNH1cNIIZDgePdIb8Wq6wEDTzFzAvfw5BPhJ2rVaChV9P 6d25htXLy5FU/qvomiy1C+ZskzbZPKGDNgr8lC/MPeNgLi0d/ps2Rgut/CGjKreW UiBmp3xslizR2/WhpRrcz0VLYxdNolfPY0odpgXkvQSEqGiZ1gOw5OQIN0f8HMiL nOXnnxFVgdO/I/x9X2DwKAGwuts/GSeWOHdeNxvflyDGEYJHt9YMT7kXcJ0/dl6z QSNHDoCMzMkxBCX23mlgY8pDSjw0Lqud0HDIChi1DFuNk7m1SfMIKGOn0ZAPsNqX RuMiLCMOPzdE8BBBpKFwZFtx0zyC78xAOBK1M8DqlUexT3CBGFjOwCmGY27dLFZe 6ygdrqptb5uDOXFsw63cWSOilCnEcx7M8FDX7QjuV6EUQwvsxpeKvHZIFVlJNQCX L5F8Lig/y4Q9iCjGiu3oT5zPuuEXPhKkyPsIeM9lC+zP/eC8rL4= =E7lp -----END PGP SIGNATURE----- ```
To view all past canaries, see:
- <https://www.buskill.in/category/Canary/>
What is BusKill?
BusKill is a laptop kill-cord. It's a USB cable with a magnetic breakaway that you attach to your body and connect to your computer.
| [!What is BusKill? (Explainer Video)](https://www.buskill.in/#demo) | |:--:| | Watch the BusKill Explainer Video for more info youtube.com/v/qPwyoD_cQR4 |
If the connection between you to your computer is severed, then your device will lock, shutdown, or shred its encryption keys -- thus keeping your encrypted data safe from thieves that steal your device.
- samcurry.net Hacking Millions of Modems (and Investigating Who Hacked My Modem)
Two years ago, something very strange happened to me while working from my home network. I was exploiting a blind XXE vulnerability that required an external HTTP server to smuggle out files, so I spun up an AWS box and ran a simple Python webserver to receive the traffic from the vulnerable server.

cross-posted from: https://reddthat.com/post/20097432
> Unbelievable...
- www.zone.eu BIMI and DMARC Can't Save You: The Overlooked DKIM Exploit
Analysts at Zone.eu, one of the leading domain registrars and web hosting providers in Europe, have observed a vulnerability affecting the global e-mail ecosystem, stemming from unaddressed warnings in the DomainKeys Identified Mail (DKIM) standard that puts billions of users in risk. This is not an...

- 16years.secvuln.info 16 years of CVE-2008-0166 - Debian OpenSSL Bug
Many DKIM setups used cryptographic keys vulnerable to the 2008 Debian OpenSSL Bug (CVE-2008-0166) in 2024.

Today, 16 years ago, Debian published a security advisory announcing CVE-2008-0166, a severe bug in their OpenSSL package that effectively broke the random number generator and limited the key space to a few ten thousand keys. The vulnerability affected Debian+Ubuntu between 2006 and 2008. In 2007, an email signature system called DKIM was introduced. Is it possible that people configured DKIM in 2007, never changed their key, and are still vulnerable to CVE-2008-0166?
https://mastodon.social/@hanno/112427156548148984
- arstechnica.com Novel attack against virtually all VPN apps neuters their entire purpose
TunnelVision vulnerability has existed since 2002 and may already be known to attackers.

-
How well can an employer be certain of a remote employee's geographical location?
cross-posted from: https://lemmy.ml/post/15178977
> FWIW, this isn't to do with me personally at all, I'm not looking to do anything dodgy here, but this came up as a theoretical question about remote work and geographical security, and I realised I didn't know enough about this (as an infosec noob) > > Presuming: > * an employer provides the employee with their laptop > * with security software installed that enables snooping and wiping etc and, > * said employer does not want their employee to work remotely from within some undesirable geographical locations > > How hard would it be for the employee to fool their employer and work from an undesirable location? > > I personally figured that it's rather plausible. Use a personal VPN configured on a personal router and then manually switch off wifi, bluetooth and automatic time zone detection. I'd presume latency analysis could be used to some extent?? But also figure two VPNs, where the second one is that provided by/for the employer, would disrupt that enough depending on the geographies involved? > > What else could be done on the laptop itself? Surreptitiously turn on wiki and scan? Can there be secret GPSs? Genuinely curious!
- lyra.horse Stealing your Telegram account in 10 seconds flat
Say you handed me your phone, what’s the worst I could do in 10 seconds?
-
A doubt in encryption

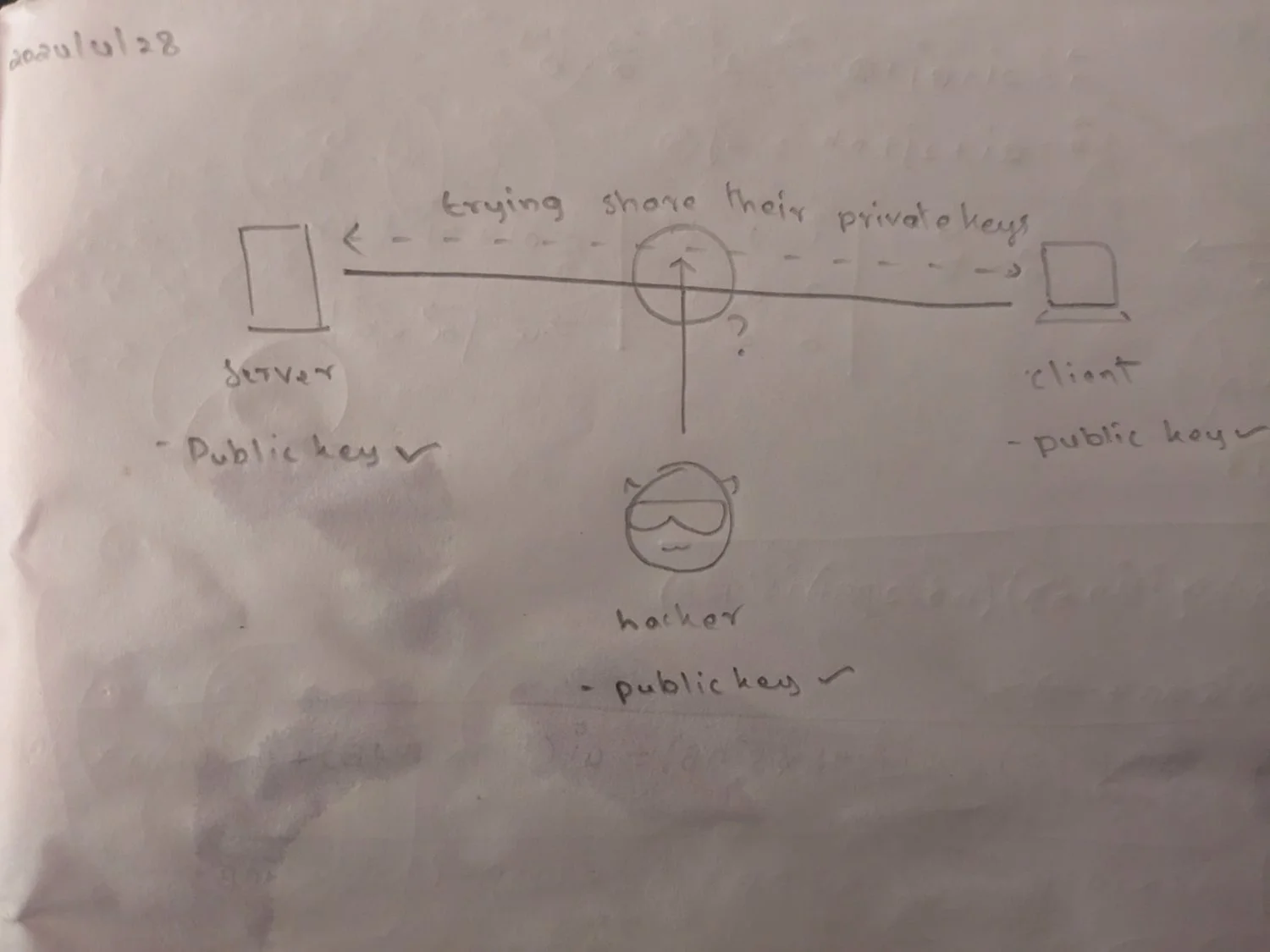
There’s a server, a client, and a hacker in a network. For encryption, the client and the server need to share their private keys. Wouldn’t the hacker be able to grab those during their transmission and decrypt further messages as they please?
- www.sciencedaily.com Computer scientists unveil novel attacks on cybersecurity
Researchers have found two novel types of attacks that target the conditional branch predictor found in high-end Intel processors, which could be exploited to compromise billions of processors currently in use.

cross-posted from: https://infosec.pub/post/11554206
> Researchers have found two novel types of attacks that target the conditional branch predictor found in high-end Intel processors, which could be exploited to compromise billions of processors currently in use.
- www.bankinfosecurity.com After XZ Utils, More Open-Source Maintainers Under Attack
Major open-source software projects are warning that more pieces of code than XZ Utils may have been backdoored by attackers, based on ongoing supply-chain attack

cross-posted from: https://infosec.pub/post/11143989
> Fresh Social Engineering Attacks Resemble Tactics Used Against XZ Utils MaintainerMajor open-source software projects are warning that more pieces of code than XZ Utils may have been backdoored by attackers, based on ongoing supply-chain attack attempts that have targeted "popular JavaScript projects," apparently seeking to trick them into sharing code maintainer rights.
-
PuTTY priority high vulnerability CVE-2024-31497
hachyderm.io Simon Tatham (@[email protected])We've released #PuTTY version 0.81. This is a SECURITY UPDATE, fixing a #vulnerability in ECDSA signing for #SSH. If you've used a 521-bit ECDSA key (ecdsa-sha2-nistp521) with any previous version of PuTTY, consider it compromised! Generate a new key pair, and remove the old public key from authori...
We've releasWe've released #PuTTY version 0.81. This is a SECURITY UPDATE, fixing a #vulnerability in ECDSA signing for #SSH.
If you've used a 521-bit ECDSA key (ecdsa-sha2-nistp521) with any previous version of PuTTY, consider it compromised! ed #PuTTY version 0.81. This is a SECURITY UPDATE, fixing a #vulnerability in ECDSA signing for #SSH.
If you've used a 521-bit ECDSA key (ecdsa-sha2-nistp521) with any previous version of PuTTY, consider it compromised!
https://www.chiark.greenend.org.uk/~sgtatham/putty/wishlist/vuln-p521-bias.html
- checkmarx.com New Technique Detected in an Open Source Supply Chain Attack
In a recent attack campaign, cybercriminals were discovered cleverly manipulating GitHub's search functionality, and using meticulously crafted repositories to distribute malware.

- www.bleepingcomputer.com New Spectre v2 attack impacts Linux systems on Intel CPUs
Researchers have demonstrated the "first native Spectre v2 exploit" for a new speculative execution side-channel flaw that impacts Linux systems running on many modern Intel processors.

cross-posted from: https://infosec.pub/post/10912691
> Researchers have demonstrated the "first native Spectre v2 exploit" for a new speculative execution side-channel flaw that impacts Linux systems running on many modern Intel processors. [...]
-
Where The Wild Things Are: Brute-Force SSH Attacks In The Wild And How To Stop Them
https://discuss.systems/@ricci/112247553557306560
-
GParted Live Is Now Patched Against the XZ Backdoor, Powered by Linux Kernel 6.7
9to5linux.com GParted Live Is Now Patched Against the XZ Backdoor, Powered by Linux Kernel 6.7 - 9to5LinuxGParted Live 1.6.0-3 live system based on the GParted free partition manager is now available for download to address the XZ backdoor.

-
Thoughts on the xz backdoor: an lzma-rs perspective | Blog
gendignoux.com Thoughts on the xz backdoor: an lzma-rs perspective | Blog | Guillaume EndignouxMany discussions about open source dependencies and maintenance happened in the last month.Two posts caught my eye in the Rust ecosystem: Sudo-rs dependencie...
-
Security advisory for the standard library (CVE-2024-24576)
blog.rust-lang.org Security advisory for the standard library (CVE-2024-24576) | Rust BlogEmpowering everyone to build reliable and efficient software.

- www.bleepingcomputer.com Critical Rust flaw enables Windows command injection attacks
Threat actors can exploit a security vulnerability in the Rust standard library to target Windows systems in command injection attacks.

-
Today marks the 10th anniversary of the Heartbleed vulnerability in OpenSSL, which had the same ultimate root cause as recent XZUtils backdoor incident
The XZ Utils backdoor, discovered last week, and the Heartbleed security vulnerability ten years ago, share the same ultimate root cause. Both of them, and in fact all critical infrastructure open source projects, should be fixed with the same solution: ensure baseline funding for proper open source maintenance.
-
Amazon storing classified US government documents improperly

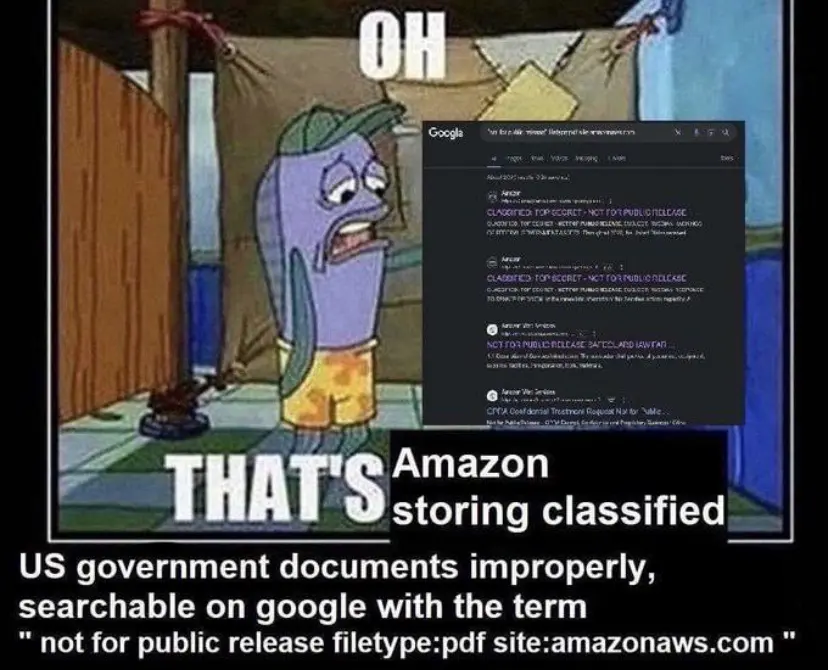
https://wetdry.world/@ari/112230288896956003
-
High Court orders temporary suspension of Telegram's services in Spain
Spain's High Court has ordered the suspension of messaging app Telegram's services in the country after media companies complained it was allowing users to upload their content without permission, according to a court source.
The use of Telegram in Spain will be temporarily suspended from Monday after a request by media firms including Atresmedia (A3M.MC), opens new tab, EGEDA, Mediaset (GETVF.PK), opens new tab and Telefonica (TEF.MC), opens new tab.
Judge Santiago Pedraz agreed to block Telegram's services in Spain while the claims are investigated. It will be the responsibility of mobile phone providers to block Telegram's services, the court source said.
Telegram is the fourth most-used messaging service in Spain, according to competition watchdog CNMC. It was used by nearly 19% of Spaniards surveyed by CNMC.
- www.bleepingcomputer.com SIM swappers hijacking phone numbers in eSIM attacks
SIM swappers have adapted their attacks to steal a target's phone number by porting it into a new eSIM card, a digital SIM stored in a rewritable chip present on many recent smartphone models.

- www.eff.org Debunking the Myth of “Anonymous” Data
Today, almost everything about our lives is digitally recorded and stored somewhere. Each credit card purchase, personal medical diagnosis, and preference about music and books is recorded and then used to predict what we like and dislike, and—ultimately—who we are. This often happens without our...

Today, almost everything about our lives is digitally recorded and stored somewhere. Each credit card purchase, personal medical diagnosis, and preference about music and books is recorded and then used to predict what we like and dislike, and—ultimately—who we are.
This often happens without our knowledge or consent. Personal information that corporations collect from our online behaviors sells for astonishing profits and incentivizes online actors to collect as much as possible. Every mouse click and screen swipe can be tracked and then sold to ad-tech companies and the data brokers that service them.
In an attempt to justify this pervasive surveillance ecosystem, corporations often claim to de-identify our data. This supposedly removes all personal information (such as a person’s name) from the data point (such as the fact that an unnamed person bought a particular medicine at a particular time and place). Personal data can also be aggregated, whereby data about multiple people is combined with the intention of removing personal identifying information and thereby protecting user privacy.
Sometimes companies say our personal data is “anonymized,” implying a one-way ratchet where it can never be dis-aggregated and re-identified. But this is not possible—anonymous data rarely stays this way. As Professor Matt Blaze, an expert in the field of cryptography and data privacy, succinctly summarized: “something that seems anonymous, more often than not, is not anonymous, even if it’s designed with the best intentions.”
- www.wired.com How the Pentagon Learned to Use Targeted Ads to Find Its Targets—and Vladimir Putin
Meet the guy who taught US intelligence agencies how to make the most of the ad tech ecosystem, "the largest information-gathering enterprise ever conceived by man."
In its 10 years of operation, Grindr had amassed millions of users and become a central cog in gay culture around the globe.
But to Yeagley, Grindr was something else: one of the tens of thousands of carelessly designed mobile phone apps that leaked massive amounts of data into the opaque world of online advertisers. That data, Yeagley knew, was easily accessible by anyone with a little technical know-how. So Yeagley—a technology consultant then in his late forties who had worked in and around government projects nearly his entire career—made a PowerPoint presentation and went out to demonstrate precisely how that data was a serious national security risk.
As he would explain in a succession of bland government conference rooms, Yeagley was able to access the geolocation data on Grindr users through a hidden but ubiquitous entry point: the digital advertising exchanges that serve up the little digital banner ads along the top of Grindr and nearly every other ad-supported mobile app and website. This was possible because of the way online ad space is sold, through near-instantaneous auctions in a process called real-time bidding. Those auctions were rife with surveillance potential. You know that ad that seems to follow you around the internet? It’s tracking you in more ways than one. In some cases, it’s making your precise location available in near-real time to both advertisers and people like Mike Yeagley, who specialized in obtaining unique data sets for government agencies.
- www.nist.gov NIST Releases Version 2.0 of Landmark Cybersecurity Framework
The agency has finalized the framework’s first major update since its creation in 2014.

-
Vehicle thefts - Insecure vehicles should be banned, not security tools like the Flipper Zero
saveflipper.ca Save FlipperSecurity research tools should be encouraged, not prohibited. Obscurity is not security.

Vehicle theft is an issue that affects us all collectively. As cybersecurity and technology professionals, we recognize the importance of acting rapidly to reduce its impact on Canadians. That being said, we believe the federal government’s proposal, particularly the prohibition of security research tools, is ill-advised, overbroad and most importantly, will be counterproductive.
- security-list.js.org Security List
Curated lists of tools, tips and resources for protecting digital security and privacy

-
Things that have been happening to me too often lately
- I am denied read-only access to some websites because I use a VPN. This makes no sense at all, but it happens anyway.
- I am not allowed to register in some forums because I use a VPN. Because everyone knows that anyone who uses a VPN is a serious criminal. There is no other option.
- I am subsequently banned from forums because the moderators realise that my IP address is not unique because I use a VPN. My posts don't matter at all, IP addresses obviously unambiguously identify every person on this planet.
- I'm supposed to confirm that I'm not a robot because I use a VPN. The fact that the company asking for these confirmations (usually Google) is itself sending robots marauding through the internet doesn't matter, because Google is Google and I'm just a bloke with a VPN.
Guys, a VPN is self-defence. A website banning VPNs is like a brothel banning condoms. I mean, of course the house rules apply, but I'd like to see a bit more judgement. What's happening right now is ridiculous and hardly does justice to the security aspect of these "tests". If you find yourself as a contributor to this list, I urge you to stop. I am not a bad guy. All I do is use a VPN.
Thank you.
-
If the Internet where to be redesigned, what would you change to improve security?
The Internet was concieved decades ago. In hindsight, many bad design choices were made. Given what was known at the time it's still blows my mind how well it has aged. There are some
Hypothetical scenario: what design choices would we change security wise if we had the opportunity to redesign the Internet from scratch today? Or to tackle the problem the other way around: what are the bad design choices for Internet security that we are stuck with today, unfixible without starting over?
-
The state of software security is dire. If we only look at the past year, if you ran industry-standard software like Ivanti, MOVEit, Outlook, Confluence, Barracuda Email Security Gateway, Citrix NetScaler ADC, and NetScaler Gateway, chances are you got hacked. Even companies with near-infinite resources (like Apple and Google) made trivial “worst practice” security mistakes that put their customers in danger. Yet we continue to rely on all these products.
Software is now (rightfully) considered so dangerous that we tell everyone not to run it themselves. Instead, you are supposed to leave that to an “X as a service” provider, or perhaps just to “the cloud.” Compare this to a hypothetical situation where cars are so likely to catch fire that the advice is not to drive a car yourself, but to leave that to professionals who are always accompanied by professional firefighters.
The assumption is then that the cloud is somehow able to make insecure software trustworthy. Yet in the past year, we’ve learned that Microsoft’s email platform was thoroughly hacked, including classified government email. (Twice!) There are also well-founded worries about the security of the Azure cloud. Meanwhile, industry darling Okta, which provides cloud-based software that enables user log-in to various applications, got comprehensively owned. This was their second breach within two years. Also, there was a suspicious spate of Okta users subsequently getting hacked.
Clearly, we need better software.
-
Twilio Authy Desktop app, new death date
For your convenience, now five months earlier! From an email received today, 2/13/24 *** You’re receiving this email from Twilio because our records show you’ve used the Twilio Authy Desktop app in the past.
What do you need to know?
Starting March 19, 2024, Twilio Desktop Authy apps will reach their end of life (EOL). Beyond this date, you can access most of the desktop features and functionality in the mobile Authy apps.
You may have previously seen an August 19, 2024, end of life (EOL) date for Twilio Desktop Authy apps. This date has been moved up to March 19, 2024.
What do you need to do?
Switch to the Authy app on your Apple or Google Play Store-compatible Android device to manage your Authy account and 2FA tokens.
What if you don’t take action?
If you don’t take action before March 19, 2024, you won’t be able to use, access, or migrate your Authy-based account tokens from the Twilio Authy Desktop apps nor download the Authy desktop apps from authy.com.
-
Nearly half the French population have data nabbed in massive breach
www.theregister.com 33m French citizens data stolen in healthcare billing breachPLUS: Juniper's support portal leaks customer info; Canada moves to ban Flipper Zero; Critical vulns

Nearly half the citizens of France have had their data exposed in a massive security breach at two third-party healthcare payment servicers, the French data privacy watchdog disclosed last week.
Payments outfits Viamedis and Almerys both experienced breaches of their systems in late January, the National Commission on Informatics and Liberty (CNIL) revealed, leading to the theft of data belonging to more than 33 million customers. Affected data on customers and their families includes dates of birth, marital status, social security numbers and insurance information. No banking info, medical data or contact information was compromised, the CNIL added.
"This is the first time that there has been a violation of this magnitude [in France]," Yann Padova, digital data protection lawyer and former secretary general of the CNIL told French radio network Franceinfo. Padova believes the breach is the largest in France's history.
- thehackernews.com Chinese Hackers Operate Undetected in U.S. Critical Infrastructure for Half a Decade
Chinese state-sponsored hacking group, Volt Typhoon, infiltrates U.S. critical infrastructure for over five years.

The U.S. government on Wednesday said the Chinese state-sponsored hacking group known as Volt Typhoon had been embedded into some critical infrastructure networks in the country for at least five years.
Targets of the threat actor include communications, energy, transportation, and water and wastewater systems sectors in the U.S. and Guam.


