Deputy President Rigathi Gachagua has called on MPs to bite the bullet and come out and apologise to the people rather than engaging them in hide-and-seek games.

Gabon’s military ruler risks becoming the country’s third autocratic leader if he fails to generate economic growth and return the country to democratic paths.

Ordinary Whites in Apartheid South Africa is a new book that explores how apartheid monitored and shaped white life, and how all classes of white people were complicit.

The current wave of abductions and disappearance of individuals linked to the ongoing countrywide

The current wave of abductions and disappearance of individuals linked to the ongoing countrywide

A hacker broke into systems used by Tile, the tracking company, then stole a wealth of customer data and had access to internal company tools.

We'll be documenting the events of Tuesday June 18, which will be the #OccupyParliament protest and the tabling of Finance Bill, 2024.

Combining elements of traditional and modern music has created rhythms that are unique to Senegalese music.

Campaigns used deepfakes to connect with voters rather than deception, and AI also helped them break through language barriers.

New research has found that the world’s baobab trees all evolved on Madagascar 21 million years ago. Sometime in the last 12 million years, they floated on piles of debris to Australia and Africa.

President Cyril Ramaphosa has for the moment dodged choosing a coalition partner by proposing a ‘government of national unity’ which conceivably could include parties that have diametrically opposed views on all major policy issues.

In a post to China’s popular WeChat platform last week, one writer bemoaned the shocking loss of nearly a full decade of information from the early days of the country’s domestic internet. Within hours the writer's reflections had vanished too.

Layer-2 protocol Ark is built to allow off-chain payments in a way that avoids what creator Burak Kecli referred to as "inbound liquidity" problem of Lightning.

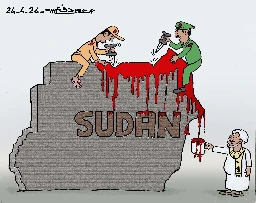
According to Lt Gen Yasir El Atta, deputy commander of the Sudanese Armed Forces (SAF),...
Fresh off a funding round from UTXO Management, Janus joins The Gwart Show. Welcome back to the Gwart Show! This week, Gwart sits down with Janus of the Bit...

At the age of 1 year 152 days, little Ace-Liam Nana Sam Ankrah from Ghana is the world’s youngest male artist.

That more than likely exists although albeit it's dropped for other things as well
You could buy a pixel 3 or even lower with the lowest storage possible to run lineageos to test if it suits your needs
- You want to experience a piece of technology you couldn't afford/were too young for
- You have backups of delisted apps that you want to use
- You want to create homebrew
Invisible planets by Ken Liu Song Dynasty Figures of Longing and Desire by Lara C.W. Blanchard
Yes in fact it has happened in this very same country https://en.wikipedia.org/wiki/Supreme_Council_for_the_Restoration_of_Democracy
The twilight princess one is pretty good too
I get that and I'm saying it's available to use rn for you to dissect and I feel like if you have such strong opinions about it the very least you could do is put your money where you mouth is and test out the network and outline all it's flaws so the community can reason about it instead of going hurr durr it's bad I hate it
They make extremely strong claims, and strong claims require strong proof. I do not see such proof anywhere. What I see is that they play fast and loose with website visitor privacy and seem to focus mainly on token hyping.
All the claims against tor and i2p are discussed in numerous academic papers and are acknowledged by the developers themselves not sure about the other projects putting that aside the network is in production rn so you could always test it and do a full writeup on all the flaws for everyone to see and discuss.Telling persons why they've decided to use tokens and not rely on pure altruism is not token hyping.
so you gonna comment on their comparison or nah?
This is “privacy for the rich” model. Unsurprisingly: poor people can’t push the token to the moon! And looking at their website it is clear they focus more on hyping the token than on actual privacy.
"Tokens will be used to reward those who put stake into the Nym ecosystem by providing services, such as operating a mixnode or validators for the Nym blockchain. Users discover service providers and attributes a service provider needs. Users may pay service providers outside of Nym directly. Alternatively, users may pay the mixnet fees directly or services may pay for or stake NYM tokens on behalf of a pool of users in order to provide services without cost to users."
It’s fascinating how they talk down Tor (“because Tor does not add timing obfuscation or cover traffic to obscure the traffic patterns in circuits”), but fail to mention i2p which solves these issues without the need for bollockschain tokens. Makes sense — Nym seems to basically be i2p with a blockchain token bolted onto it so that it can become an investment vehicle.So either they did not know about i2p, an important and reasonably well known project which has been around for almost 20 years and is very clearly in the same problem space, or they intentionally decided not to mention it because it would make them look bad. Take your pick: are they ignorant, or disingenuous? Either is a great trait for a project that aims at protecting privacy from the NSA, no less.
" I2P (‘Invisible Internet Project’) replaces Tor’s directory authority with a distributed hash table for routing. How to design a secure and private distributed hash table is still an open research question, and I2P is open to a number of attacks that isolate, misdirect, or deanonymize users. Like Tor, I2P is based on ‘security by obscurity’, where it is assumed that no adversary can watch the entire network. While security by obscurity may have been cutting-edge at the turn of the millennium, such an approach is rapidly showing its age.Nym’s cutting-edge mixnet design guarantees network anonymity and resistance to surveillance even in the face of powerful deanonymizing attacks. Unlike I2P, Nym adds decoy traffic and timing obfuscation. Rather than a centralized directory authority or distributed hash table, Nym uses blockchain technology and economic incentives to decentralize its network.The Nym mixnet can anonymize metadata even against government agencies or private companies who can monitor network links and observe the incoming and outgoing traffic of all clients and servers." Source: https://get3xnymtech.net/docs/stable/overview/index.html. Full in depth blog post comparing it against tor, vpns , i2p and other solutions in the space https://blog.nymtech.net/vpns-tor-i2p-how-does-nym-compare-8576824617b8
Can you at least read their whitepaper and make a fully informed decision instead of hoping for their downfall
It’s news about a place in the world

