- www.eff.org Hack of Age Verification Company Shows Privacy Danger of Social Media Laws
We’ve said it before: online age verification is incompatible with privacy. Companies responsible for storing or processing sensitive documents like drivers’ licenses are likely to encounter data breaches, potentially exposing not only personal data like users’ government-issued ID, but also...

>We’ve said it before: online age verification is incompatible with privacy. Companies responsible for storing or processing sensitive documents like drivers’ licenses are likely to encounter data breaches, potentially exposing not only personal data like users’ government-issued ID, but also information about the sites that they visit. > >This threat is not hypothetical. This morning, 404 Media reported that a major identity verification company, AU10TIX, left login credentials exposed online for more than a year, allowing access to this very sensitive user data. > >A researcher gained access to the company’s logging platform, “which in turn contained links to data related to specific people who had uploaded their identity documents,” including “the person’s name, date of birth, nationality, identification number, and the type of document uploaded such as a drivers’ license,” as well as images of those identity documents. Platforms reportedly using AU10TIX for identity verification include TikTok and X, formerly Twitter. > >Lawmakers pushing forward with dangerous age verifications laws should stop and consider this report. Proposals like the federal Kids Online Safety Act and California’s Assembly Bill 3080 are moving further toward passage, with lawmakers in the House scheduled to vote in a key committee on KOSA this week, and California's Senate Judiciary committee set to discuss AB 3080 next week. Several other laws requiring age verification for accessing “adult” content and social media content have already passed in states across the country. EFF and others are challenging some of these laws in court. > >In the final analysis, age verification systems are surveillance systems. Mandating them forces websites to require visitors to submit information such as government-issued identification to companies like AU10TIX. Hacks and data breaches of this sensitive information are not a hypothetical concern; it is simply a matter of when the data will be exposed, as this breach shows. > >Data breaches can lead to any number of dangers for users: phishing, blackmail, or identity theft, in addition to the loss of anonymity and privacy. Requiring users to upload government documents—some of the most sensitive user data—will hurt all users. > >According to the news report, so far the exposure of user data in the AU10TIX case did not lead to exposure beyond what the researcher showed was possible. If age verification requirements are passed into law, users will likely find themselves forced to share their private information across networks of third-party companies if they want to continue accessing and sharing online content. Within a year, it wouldn’t be strange to have uploaded your ID to a half-dozen different platforms. > >No matter how vigilant you are, you cannot control what other companies do with your data. If age verification requirements become law, you’ll have to be lucky every time you are forced to share your private information. Hackers will just have to be lucky once.
-
Google, Snap, Meta and many others are "quietly" changing privacy policies to allow for AI training | It is sneaky and possibly illegal, according to the FTC
www.techspot.com Google, Snap, Meta and many others are "quietly" changing privacy policies to allow for AI trainingEarlier this year, the Federal Trade Commission warned that companies would be sorely tempted to change the terms and conditions of their privacy statements to allow them...

-
Mullvad VPN: Fourth Infrastructure audit completed by Cure53
mullvad.net Fourth Infrastructure audit completed by Cure53 | Mullvad VPNWe contracted Cure53 with performing a security audit towards our VPN infrastructure between 3rd June 2024 and 14th June 2024, this is our fourth audit in total, second with Cure53.

-
Are there any guides, tutorials or similar on how to use Steam more privately?
cross-posted from: https://discuss.tchncs.de/post/18038249
> Are thwre guides, tutorials or similar on how to use Steam more privately? > > I'm at a point where I'd like to play certain games, but I dislike that they're exclusively available on consoles and Steam for Desktop. Steam's Privacy Policy and Terms of Service raise concerns about my personal security and privacy. I'm looking for advice on how to improve my privacy while using Steam. > > Thank you in advance! > > (I will use Steam on Linux)
- web.archive.org How TikTok Reads Your Mind (Published 2021)
It’s the most successful video app in the world. Our columnist has obtained an internal company document that offers a new level of detail about how the algorithm works.

-
SimpleX Chat Group about Privacy & Security


If you want to join the group, please send me a PM with the reason you want to and your favourite animal.
-
Proton is transitioning towards a non-profit structure
proton.me Proton is transitioning towards a non-profit structure | ProtonTo ensure our mission always comes first, Proton is transitioning to a non-profit structure and formalizing our promise of people before profits.

-
Legality of removing sim cards from cars in Australia
Does anyone know about the legality of removing the built-in sim cards from your car, specifically in Australia?
I don't intend on using any car smart-features when I get one. For context, I've never owned a car. When I do get one though, I intend to remove the sim card to prevent the car's location from being constantly tracked. All I care about in terms a cars functionality is a radio, a CD drive (Yes, I use CD's), and Bluetooth audio, so I don't think removing the sim card should affect this much, if at all. Any knowledge and advice would be appreciated, thankyou!
Update: What I was referring to is an eSim, which appears not to be in the form of a physical card. Even so, if possible, I would like to disable the functionality of this eSim assuming the car I purchase has one in-built. From my research, I cannot find anything that explicitly forbids disabling or removing Sims.
- www.macrumors.com Sonos' Privacy Policy Change Suggests It Might Sell Your Data
Popular audio company Sonos recently updated its U.S. privacy policy to make a small but notable change that seemingly puts customer data at risk. As...

-
Mullvad app without multihop x WireGuard official app
Hi guys!
Today I use Mullvad VPN on my Pixel 8 but unfortunately Mullvad team didn't enable multihop feature to use on Android app.
Use WireGuard official app and importing wireguard key file is a good approach to have multihop feature enable on Android?
-
iOS 18 now allows users to selectively share specific contacts with apps, rather than granting full or no access to all contacts as in previous versions
techcrunch.com iOS 18 cracks down on apps asking for full address book access | TechCrunchTo give users more control over the contacts an app can and cannot access, the permissions screen has two stages.
>iOS apps that build their own social networks on the back of users’ address books may soon become a thing of the past. In iOS 18, Apple is cracking down on the social apps that ask users’ permission to access their contacts — something social apps often do to connect users with their friends or make suggestions for who to follow. Now, Apple is adding a new two-step permissions pop-up screen that will first ask users to allow or deny access to their contacts, as before, and then, if the user allows access, will allow them to choose which contacts they want to share, if not all.
>For those interested in security and privacy, the addition is welcome. As security firm Mysk wrote on X, the change would be “sad news for data harvesting apps…” Others pointed out that this would hopefully prevent apps that ask repeatedly for address book access even after they had been denied. Now users could grant them access but limit which contacts they could actually ingest.
- www.macrumors.com iOS 18 and macOS Sequoia Add 'Rotate Wi-Fi Address' Option to Cut Down on Tracking
With iOS 18, iPadOS 18, and macOS Sequoia, Apple has replaced the Private Wi-Fi Address option for Wi-Fi networks with a new Rotate Wi-Fi Address...

-
Win for Free Speech! Australia Drops Global Takedown Order Case | Electronic Frontier Foundation
www.eff.org Win for Free Speech! Australia Drops Global Takedown Order CaseNo single country should be able to restrict speech across the entire internet. That's why EFF celebrates the news that Australia's eSafety Commissioner is dropping its legal effort to have content on X taken down across the globe. This development comes just days after EFF and FIRE were granted off...

cross-posted from: https://lemmy.zip/post/17061827
-
Any way to join Zoom with any privacy at all
Hello let's say you are absolutely forced to join zoom in the future, is there any way at all to have any security, such as an alternate client that can connect? I expect the answer is no besides only connecting in a browser with add ons or in a sandbox etc etc and nothing truly groundbreaking.
-
Opinions on the TP-LINK Archer AX23
cross-posted from: https://lemmy.ca/post/22775470
> I'm looking to buy a router for home use, on which I plan to install OpenWRT. After some research, I have come across the TP-LINK Archer AX23, which checks all of the boxes I have: > > > > - [x] Comparatively low price > > - [x] Supports WPA3 > > - [x] Supported by OpenWRT > > - [x] Has at least three LAN ports > > > > However, before I and my dad go and buy one, it has to pass the final test: the forums. > > > > Has anyone used this router before? What was your experience? Can I do better, or have I found the best router ever made? Please share your thoughts.
-
Is there a good way to prevent apps/programs from accessing the internet, or restrict it to VPNs only?
I'm asking for Android specifically, but I'm curious what else is out there.
For example, some apps work without internet but may use it if it's available. I might want to block that without having to turn off wifi, force stopping it, and wiping the cache/data.
Similarly, maybe I only want to use the app over a VPN and want to prevent accidentally opening it without first turning the VPN on.
-
How do people plan for their deaths in terms of account & device secrets (passwords, 2fa etc.)?
I have thought about this on and off for quite a few years now, and I was just wondering what people here have done while maintaining account / device security.
I hope people don't mind this rather morbid conversation, but how have people here planned for what will happen with their accounts, computers, self hosted things etc. in the event of their deaths? I am particularly interested in what people have planned for if they are the person in their household who is self hosting things for the household. I'm not in a living situation that allows me to self host much but it is one of the questions I've had for myself when I decide to move in with my significant other and self host more things. I don't think they could manage much of the self hosted stuff and I also don't think they can remember all of the credentials for accounts etc., is the best way of going about it sharing a keepass database or bitwarden account with them?
In regards to my accounts, I am not expecting most of my accounts to transfer, if anything I'd much rather them be deleted (and I have enabled this feature where possible). There are a few however, that I wouldn't mind leaving to someone after my passing. Is there a privacy and security preserving way of setting this up?
I guess I have just been struggling with how to do this, ideally I would want a way for accounts to transfer to someone listed in my will, but I don't think it's a good idea to give ~2-3 people a copy of my keepass databse while I am still living.
I am looking forward to hearing what people's thoughts are on this matter, and I apologize again for such a morbid topic.
-
Internet Archive is in danger

cross-posted from: https://lemmy.zip/post/16884561
> It looks like the internet archive is needed assistance, I just heard about this today and figured lemmy could help spread this message around
-
Hey
Hey @privacyguides I can't post a picture from my account on your lemmy instance. Please help.
- www.vox.com Is it ever okay to film strangers in public?
Nobody wants to be filmed without their knowledge. Why does it make up so much of the content we watch?

-
NOYB urges 11 DPAs to immediately stop Meta's abuse of personal data for AI
noyb.eu noyb urges 11 DPAs to immediately stop Meta's abuse of personal data for AInoyb urges DPAs in 11 countries to immediately stop Meta's use of personal data for undefined "AI technology"

-
DuckDuckGo AI Chat adds support for Llama 3 70B and Mixtral 8x7B

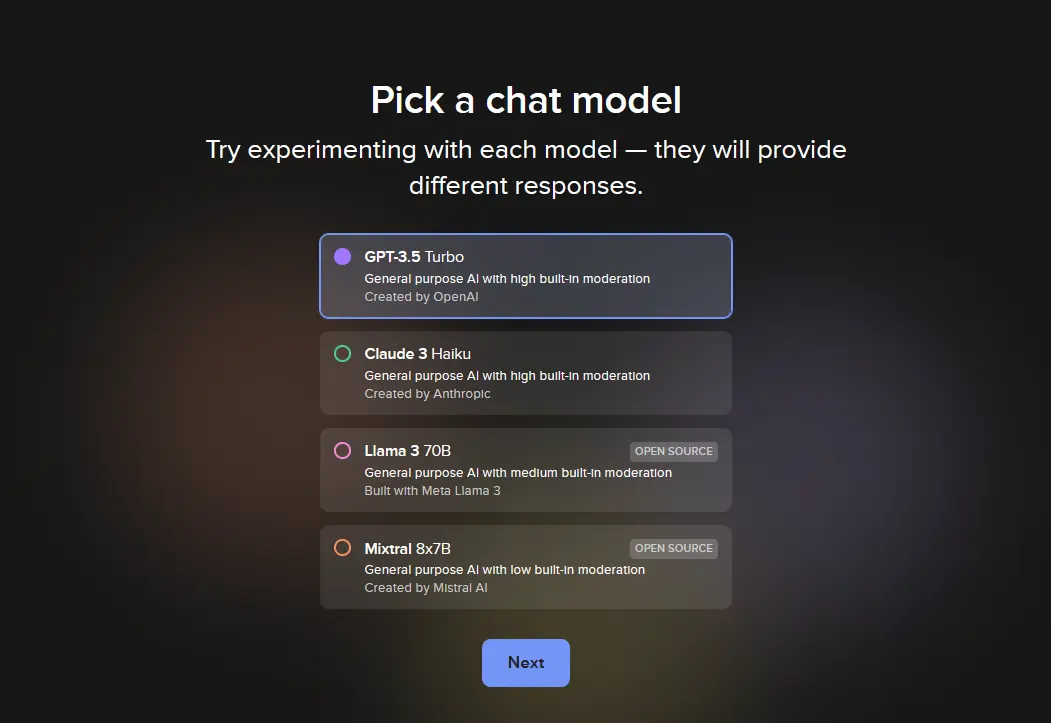
Might be helpful for those that
- don't have access to hardware that can run things locally
- understand the benefits and limitations of generative AI
Link: https://duckduckgo.com/?q=DuckDuckGo&ia=chat
As a nice coincidence, one of the first results when I searched for a news update was this discussion:
https://discuss.privacyguides.net/t/adding-a-new-category-about-ai-chatbots/17860/2
-
New cryptee update
blog.crypt.ee Document templates, massive performance improvements & more!Document templates, massive performance improvements, and tons of small new features in Cryptee Docs!

I just share it cause I like how cryptee becomes better and better with each update :) Document templates, massive performance improvements and more.
- www.patrick-breyer.de Majority for chat control possible – Users who refuse scanning to be prevented from sharing photos and links
The highly controversial indiscriminate child sexual abuse regulation (so-called chat control) could still be endorsed by EU governments after all, as France could give up its previous veto. This is reported by Euractiv and confirmed by internal documents. France considers the new "upload moderation

-
Private way to use Google Maps on iOS
Hello everyone! Long story short, I switched from CalyxOS to iOS because the Pixel 5 was too big for me.
Now that I'm on iOS, I'd like to know if there was a way to use google maps anonymously/privately.
I used to use the GMapsViewer application on Fdroid. Today the solution I've found is to use Firefox focus and go to the Google Maps site, but it's a bit of a mess to find a simple address.
Do you have another idea for me? Thanks in advance!
- arstechnica.com Google accused of secretly tracking drivers with disabilities
Google recklessly violated privacy laws to spike ad profits, lawsuit says.

-
Is CalyxVPN reputable?
I came across CalyxVPN while browsing through F-droid, it seems to be offered by the same people who make CalyxOS. I couldn't find much discourse about it online, is it reputable enough to use?
My use case would be to hide whatever I do online from my ISP (I'm not torrenting, just browsing).
And yes, I know free VPNs are untrustworthy in most cases but this seems to come from a somewhat privacy respecting background so I was curious.
-
Cookies
Newb question: what does it really mean when I click "Reject Nonessential Cookies"? Am I really being any more private by rejecting these? Just feels greasy like it's a workaround for websites to get my information anyway? Should I navigate away from any sites that suggest this cookie configuration?
-
PayPal will use your purchase information and shopping patterns to sell targeted ads
www.theverge.com PayPal is building an ad network based on your Venmo dataPayPal will collect customer data by default.

>“If you’re someone who’s buying products on the web, we know who is buying the products where, and we can leverage the data,” Grether said in a statement to the WSJ. He also said that PayPal will receive shopping data from customers using its credit card in stores.
>A PayPal spokesperson tells the WSJ that the company will collect data from customers by default while also offering the ability to opt out.
>PayPal is far from the only company to sell ads based on transaction information. In January, a study from Consumer Reports revealed that Facebook gets information about users from thousands of different companies, including retailers like Walmart and Amazon. JPMorgan Chase also announced that it’s creating an ad network based on customer spending data, while Visa is making similar moves. Of course, this doesn’t include the tracking shopping apps do to log your offline purchases, too.
-
Best bitcoin wallet when samourai is gone?
And when to buy xbt or xmr without kyc in EU when both localmonero and localbitcoin are closed?
-
Revolut vs privacy.com vs google wallet
Has anyone here used Revolut? How does it compare to privacy.com for EU users?.
Can you use the tap to pay on your phone without using Google Wallet?
- blog.thenewoil.org Is Privacy Worth It?
When I announced I would be closing my communities earlier this year, a curious thing happened: a surprising number of regulars replied w...

-
Phone number services
I am searching for a job and require my phone number to be included on my resume. Is there a service available in the EU (excluding the UK) that can provide this.
- arstechnica.com New Windows AI feature records everything you’ve done on your PC
Recall uses AI features "to take images of your active screen every few seconds."

-
Google Photos/Gmail AI data removal
Hello, with the new AI features being added into Googles services I was thinking of maybe starting a thread about how to remove data from the affected services. I feel like simply deleting my photos from Google Photos most likely wouldn't be enough of a measure to ensure my images does not get affected or used in these AI features.
Is there any way to ensure that Google properly removes your data after deleting it?
Sources: https://www.youtube.com/watch?v=iinwIYt1IzM https://www.techradar.com/computing/artificial-intelligence/google-io-showcases-new-ask-photos-tool-powered-by-ai-but-it-honestly-scares-me-a-little https://arstechnica.com/gadgets/2024/05/gmails-ai-powered-email-summaries-can-dig-through-your-inbox-for-you/
-
Privacy services and non privacy payments options
Why most services that want to protect user privacy. Also those on privacyguides, don't have anonymous payment methods like cryptocurrencies? I pay for a few such services like email or cloud etc. but I don't know if it makes sense if my bank knows I'm using it anyway so they can sell that info to advertisers, gov, etc. In EU services like mysudo or privacy.com are unavailabe so I can't use masked cards. What is then the profit of using such services if I don't pay for them with cryptocurrencies and they can be easily linked to me?
- uk.pcmag.com Dangerous? Signal Blasts Google Effort to Use AI to Scan for Scam Phone Calls
One of the leaders of the private messaging app Signal calls the feature 'dangerous' because it could potentially spy on users.
>Google’s AI model will potentially listen in on all your phone calls — or at least ones it suspects are coming from a fraudster. > >To protect the user’s privacy, the company says Gemini Nano operates locally, without connecting to the internet. “This protection all happens on-device, so your conversation stays private to you. We’ll share more about this opt-in feature later this year,” the company says.
>“This is incredibly dangerous,” says Meredith Whittaker, the president of a foundation for the end-to-end encrypted messaging app Signal. > >Whittaker —a former Google employee— argues that the entire premise of the anti-scam call feature poses a potential threat. That’s because Google could potentially program the same technology to scan for other keywords, like asking for access to abortion services. > >“It lays the path for centralized, device-level client-side scanning,” she said in a post on Twitter/X. “From detecting 'scams' it's a short step to ‘detecting patterns commonly associated w/ seeking reproductive care’ or ‘commonly associated w/ providing LGBTQ resources' or ‘commonly associated with tech worker whistleblowing.’”
-
Anyone familiar with the "No Trace Project"?
www.notrace.how No Trace ProjectNo trace, no case. A collection of tools to help anarchists and other rebels understand the capabilities of their enemies, undermine surveillance efforts, and ultimately act without getting caught.
I've just been clued into this and I'd like to know if anyone can give me an idea of the quality of the information contained therein. Thanks in advance--I hope you're well today!