Hacking
-
Do these methods work to view private IG profiles ?
https://inscaptions.com/how-to-see-private-accounts-on-instagram-using-inspect/
https://techcult.com/how-to-access-private-instagram-inspect-element/
I don’t know anything about programming, and sadly I can’t differentiate between rubbish webpages and the real deal when it comes to stuff like that..
I also read about a couple of ios shortcuts that claim to be able to download private Instagram posts if you have the link to it.. is it true?
- samcurry.net Hacking Millions of Modems (and Investigating Who Hacked My Modem)
Two years ago, something very strange happened to me while working from my home network. I was exploiting a blind XXE vulnerability that required an external HTTP server to smuggle out files, so I spun up an AWS box and ran a simple Python webserver to receive the traffic from the vulnerable server.

-
Giving Away Steam Account (I'm Locked Out)
So I have an old Steam account I had for years. Will give away account information to someone if you think you can get in.
Here's the situation: I changed my email to a forwarding service. so it's [email protected] However, the forwarding service shut down and is no longer functioning, so I'm locked out of the account. I don't even know the email address that was generated for me because the service is gone. However if there's anyone here that thinks they can get in, I'm happy to send along the login information I do have. DM me if interested.
-
Iphone event log to check potential hack
Apologies is this seems somewhat weird, I was using the reddit app on my iphone when I clicked on a tag in my search history and at the same time I noticed my flash go off on my phone. I suppose this could have been some strange hardware issue in my phone, but I suspected it took a photo. I checked my photo stream and there was nothing new. There is no log of events on my phone I know of, but I wondered if it was intentional. Curious if anyone here has any idea if it could have been something intentional (it taking a photo), or maybe some log info source I could check to see if it was legitimate hack.
-
Best fuzzing tool
I'm trying to find a good fuzzing tool for testing my web applications and was wondering what people would recommend. I'm trying to find one that is open source, free, and doesn't use proprietary stuff. It seems like Google's OSSFuzz is the closest option to what I'm looking for, but it uses Google cloud :/
-
Bluetooth security flaws reveals all devices launched after 2014 can be hacked
Security researchers have discovered new Bluetooth security flaws that allow hackers to impersonate devices and perform man-in-the-middle attacks.
The vulnerabilities impact all devices with Bluetooth 4.2 through Bluetooth 5.4, including laptops, PCs, smartphones, tablets, and others.
Users can do nothing at the moment to fix the vulnerabilities, and the solution requires device manufacturers to make changes to the security mechanisms used by the technology.
Research paper: https://dl.acm.org/doi/pdf/10.1145/3576915.3623066
Github: https://github.com/francozappa/bluffs
CVE: https://nvd.nist.gov/vuln/detail/CVE-2023-24023
-
New plugins coming soon on aluminum-ice/pwnagotchi: ntfy, Mastodon, handshake-m
cross-posted from: https://lemmy.cat/post/5756727
> Over the last few weeks I've been working on a number of plugins which I hope will be available in the next pwnagotchi release. > > - nfty: send and receive notifications and alerts to devices via ntfy service. > - mastodon: periodically post status updates of your pwnagotchi on Mastodon > - handshake-m: view and manage handshake captures via web UI. > - wpa-cracked-insert: generates a .pcap.cracked file for displaying passwords in webgpsmap. > > These plugins are also initially available on my own repo with more info on how to use them: https://codeberg.org/retiolus/pwnagotchi-plugins > > I hope this kind of thing will give the project some new energy :) >
-
TV hardware hacking
Hey all,
I am looking into hacking TVs. Its well known they run linux most of the time, so we should be able to do some fun stuff with them.
I've found some guides, clips and other reference material online, but it isn't much. Do any of you guys have some reference material to help me on my learning journey?
-
Info from 5.6 million patient visits among data stolen in ransomware attack on Ontario hospitals
> A 3rd set of data has been published on the dark web, site says, as OPP continue investigation
-
Update and reformatting of Pwnagotchi plugin that publishes regularly on Mastodon!
github.com Update mastodon.py by retiolus · Pull Request #44 · evilsocket/pwnagotchi-plugins-contribUpdate and reformatting of the plugin, which was no longer working, was not optimised and did not provide enough information in the logs. Among other things, it no longer uses the Mastodon account ...

- www.theregister.com India's biggest tech centers named as cyber crime hotspots
Global tech companies' Bharat offices attract the wrong sort of interest

-
22-year anniversary of Project Blinkenlights
Video
Click to view this content.
cross-posted from: https://feddit.de/post/3322209
Insensitive joke
A building you would have liked to stand next to on September 11, 2001.
NewPipe-compatible link to the video / YT / Piped
Hard-to-read scrolling text in my tribute video
On September 11, 2001, NYC was swept by the tragic collapse of two giant shopping malls conference centers while downtown Berlin was delighted to see a building come to life. The Blinkenlights, an array of 144 lightbulbs inside the Teacher's House on Alexanderplatz, made its debut on this fateful day. Chaos Computer Club, a German group of hackers and technology enthusiasts, had taken over the building prior to its planned reconstruction. Celebrating their 20th anniversary and amazing the public with their technical skills, the club installed floodlights behind the windows in the upper eight floors, lighting them up with animated content controlled over the network. People connected to the Internet would submit 20fps, 18x8 animations via email to take part in a pixel art contest, or have a love letter displayed at will. This is where this “BlinkenPaint” program came into play. GSM integration also enabled anyone to play a recreation of Pong, as well as remote debugging. The installation instantly became popular with music videos filmed in front of and inside it, and thousands of people came to the February 23 farewell party. The club released their hardware blueprints and source code to the public, enabling reconstructions of this project elsewhere.
In September 2002, the CCC created another installation, the “Blinkenlights Arcade”, to celebrate the “White Night” festival in Paris. The French National Library sprang to life with a 20x26 array of lightbulbs. Forgoing the abuse of relays in the original Blinkenlights, solid-state circuitry allowed 8 stages of grayscale, enhancing the look of GSM-controlled games such as Pong or Tetris, as well as music visualizations during the October 5 party. In 2008, the Toronto City Hall was lit with a 960-pixel, 16-step grayscale screen during this festival.
By the way, the title of the installation references a 1950s meme text hung in computer rooms worldwide, exclaiming to “turisten und nonteknischen lookenspeepers” that “das komputermaschine ist nicht für der gefingerpoken und mittengraben […] für gewerken bei dummkopfen” and encouraging them to “relaxen und watschen der blinkenlichten” instead. Someone will surely have posted the entire copypasta in the comments. Also look there for clarifications and corrections of any mistakes in this text.
Over the past 20 years, giant LED screens have become ubiquitous in cities, and the idea of a display this size does not seem as outlandish anymore. Nevertheless, most display advertisements round the clock, and having the public play games and submit love letters remains unique to Blinkenlights and the installation should be remembered to this day.
-
breach not on the taxis?
does anyone have any idea what the new breach forums onion is? or why tor taxi and such don't share it anymore? is tor taxi or breech sussy?
-
Your favorite hacking / cyber podcasts?
I'm a big fan of Darknet Diaries and Smashing Security. I'm all the way caught up on them though so I'm wondering if there are any others out there I'm missing out on?
If this post gets a decent number of comments I'll create a list here of every podcast recommended.
-
Reflections on Trusting Trust
The linked paper was pointed out to me during a discussion about trusting executables built from source. Perhaps this paper is a well-known document in the hacking community, but I thought it was quite interesting and thought I'd share it.
The document describes how the author created a bugged C compiler that would compile UNIX code in which the "login" command would insert a backdoor.
> The actual bug I planted in the compiler would match code in the UNIX "login" command. The re- placement code would miscompile the login command so that it would accept either the intended encrypted password or a particular known password. Thus if this code were installed in binary and the binary were used to compile the login command, I could log into that system as any user.
The author also describes strategies to build such bugged compiler in a way that would be very difficult to detect.
The document ends with a moral statement about hacking with a perspective from 1984 which is also an interesting read.
- hackaday.com Review: Beepy, A Palm-sized Linux Hacking Playground
In the long ago times, when phones still flipped and modems sang proudly the songs of their people, I sent away for a set of Slackware CDs and embarked on a most remarkable journey. Back then, runn…
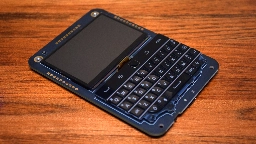
You had me at BlackBerry keyboard!
-
what is the best way to report internal security concerns in a corporate environment
I have repeatedly fund security concerns when working on internal applications. Simple things like sql injection, hard coded credentials, and privileged containers being run as the standard. I brought these up with my team lead, but he says that since its in the dev environment, it does not matter. To me, that is the totally wrong attitude to have about security. We should teach our developers how to not make these mistakes and fix them as we find them. Should I go over his head to report it to other managing parties? I want to say more, but am being as vague as possible just in case. How do I go about reporting internal vulnerabilities in a responsible way that won't make everyone hate me? I honestly believed that people would be happy to hear about their problems from me rather than get exploited but it does not seem to be the culture here.
-
SSRF help ?
Anybody know any good resources to learn about SSRF ? More than just a library of requests to have burp try. Id like to get a better understanding of crafting my own SSRFs.
- www.pbs.org How communism turned Cuba into an island of hackers and DIY engineers
Just outside Havana, in the childhood bedroom of illustrator Edel Rodriguez, a washing machine engine welded to a boat propeller has become a makeshift fan. This kind of cobbled-together contraption is common in Cuba. So are stoves that run on diesel from trucks, satellite dishes made of garbage can...
-
We can't be like the reddit community.
The hacking community on Reddit is imo one of the most toxic communities. Nearly every question someone asks the top comment is someone talking shit about OP, insulting them, or just gatekeeping hacking in general. We were all new once, if someone asks a script kiddie question, then help them out and point them in the right direction.
-
2600 Madrid! – 2600 Madrid Meeting - WorldWide 2600 Meetings
cross-posted from: https://lemmy.ml/post/1633529
> #2600 meetings worldwide, and of course 2600.Madrid in 7 days! https://2600.Madrid gemini://2600.Madrid matrix: #2600_Madrid:hispagatos.org mobilizon: https://eventos.hispagatos.org/events/608a824b-9c9f-473b-bc9f-9c3b115cbed9 PLEASE RESERVE SO WE CAN TELL THE BAR how many people we are going to be #HappyHacking #HackingIsNotACrime #2600Madrid https://2600.com
-
Hitting the Books: How hackers turned cybercrime into a commercial service
www.engadget.com Hitting the Books: How hackers turned cybercrime into a commercial service | EngadgetIn "Fancy Bear Goes Phishing", Yale Law professor Dr.
-
Ukraian hackers take down Russian banks service provider
www.bleepingcomputer.com Ukrainian hackers take down service provider for Russian banksA group of Ukrainian hackers known as the Cyber.Anarchy.Squad claimed an attack that took down Russian telecom provider Infotel JSC on Thursday evening.

-
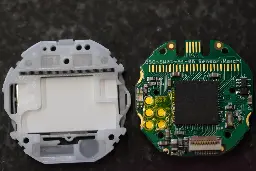
The HDMI SSD1306 that EVERYONE needs. Hacking done proper.
From the article: > You have to register to download the HDMI spec which is more effort than I have for this...
-
How I hacked a hardware crypto wallet and recovered $2 million

YouTube Video
Click to view this content.
-
Does brute-forcing SSH logins for random IPs have a reasonable chance of being profitable for the attackers?
I was looking at my /var/log/auth.log in my personal computer and VPS, and I can see thousands of failed SSH attempts over the past few days. Looking at the attempted logins, I suppose that someone is using a database and trying out common default username/password combinations to attack random IP addresses. I also see that they try this for many different ports.
This approach of attack appears to me to be very very very unlikely to return anything of value. They may as well just try generating bitcoin private keys randomly until they find a wallet with something in it.
Are these 'hackers' just playing the lottery and wasting their resources? Or is this a strategy that somehow works reasonably often?
-
Anyone used TryHackMe? It's pretty fun so far
I like how they have in-browser VMs and optional OpenVPN for using your own stuff. Also their lessons are fun so far. I'm doing Pre-Security path just to brush up on old stuff first.
-
Need to take down r/antipsychiatry
ISO if someone to help take down an anti mental health services subreddit. Remuneration to be discussed layer______
-
Linux Privilege Escalation — Three Easy Ways to Get a Root Shell
publication croisée depuis : https://lemmy.ml/post/75899
> How to go from a low privilege user to root on a Linux system through 3 simple techniques.
-
Windows Kernel Debugging & Exploitation Part 1 - Environment Setup
hacklido.com How I tried harder and passed my OSCP exam first try, with no experience!Introduction Hello amazing hackers! I am really happy to see you here because i was afraid to write this article. I do not want to boast, and it feels like...
-
Did anyone already work on an evil usb project?
spyboy.blog Make Your Own Evil USBRecently, someone asked how to make your own “Evil USB,” and I promised to make a how-to on this topic. In addition, it would be nice to have something related on our WonderHowTo world.…

Hi, I'm working on shool project for creating and using a evil usb to see if it's still a thing. The thing I cannot find the right usb, because almost every models can't be bought anymore... Does someone know another option? Like maybe making a custom usb? I don't want to use phone or else, just an usb
- ddosecrets.substack.com Hacktivism, Leaktivism and the Future
The future will be written, as it always is, by those who are willing to engage.
> Yet despite all the unprecedented recent events, 2020 and 2021 also feel very familiar to some of us. The mood has been similar to that of Anonymous' highs in 2010, 2011 and 2012. Instead of groups like LulzSec, we have people like Keyser Soze and groups like APT-69420. Documents and source code spilled onto the internet, to the horror of governments and corporations. And inevitably, the raids began and indictments began to be returned.
> Ten years ago, WikiLeaks fought censorship by making it easy to mirror their site and leaks. Today, while Distributed Denial of Secrets (DDoSecrets) faces the scrutiny of the U.S. government and continues to fight our server seizure, we're fighting censorship by making not just our data, but our model easy to mirror. Groups like DDoSecrets can be dismantled if governments are truly determined to oppress and suppress, but we're as easily replicated as the Anonymous model or the APT-69420 model. The world can no longer be rid of hacktivists or leaktivists, not as long as people are willing.
-
Getting root access to fix a doorbell
The article does more than get root access. I like how the author bought a copy of the doorbell to work on.