
- www.theverge.com Microsoft left internal passwords exposed in latest security blunder
An internal Azure-hosted server was left without password protection.

cross-posted from: https://lemmy.zip/post/13403067
> Microsoft left internal passwords exposed in latest security blunder > > > An internal Azure-hosted server was left without password protection.
-
Galactical Bug Hunting: How we discovered new issues in CD Projekt Red’s Gaming Platform
www.anvilsecure.com Galactical Bug Hunting: How we discovered new issues in CD Projekt Red's Gaming Platform - Anvil SecureAs a researcher I often run into situations in which I need to make a compiled binary do things that it wouldn’t normally do or change the way it works in some way. Of course, if one…

-
Wifi credential dumping
www.r-tec.net WIFI Credential Dumping: Techniques to retrieve the PSK from a workstation post-compromiseThis blog won't dive into any of the mentioned WIFI attacks, but will highlight techniques to retrieve the PSK from a workstation post-compromise instead.

- www.lasso.security Diving Deeper into AI Package Hallucinations
Lass Security's recent research on AI Package Hallucinations extends the attack technique to GPT-3.5-Turbo, GPT-4, Gemini Pro (Bard), and Coral (Cohere).

-
Security Advisory: Systems with a SONIX Technology Webcam vulnerable to DLL hijacking attack allowing attackers to execute malicious DLL and escalate privileges
herolab.usd.de usd-2023-0029 - usd HeroLabAdvisory ID: usd-2023-0029 | Product: SONIX Technology Webcam | Vulnerability Type: CWE 732 - Incorrect Permission Assignment for Critical Resource

-
unch 😗: Hides message with invisible Unicode characters
github.com GitHub - dwisiswant0/unch: Hides message with invisible Unicode charactersHides message with invisible Unicode characters. Contribute to dwisiswant0/unch development by creating an account on GitHub.
-
Gram - Self-hosted Threat Modeling Webapp
github.com GitHub - klarna-incubator/gram: Gram is Klarna's own threat model diagramming toolGram is Klarna's own threat model diagramming tool - klarna-incubator/gram
-
Kobold letters – Why HTML emails are a risk to your organization
lutrasecurity.com Kobold letters – Lutra SecurityAnyone who has had to deal with HTML emails on a technical level has probably reached the point where they wanted to quit their job or just set fire to all the mail clients due to their inconsistent implementations. But HTML emails are not just a source of frustration, they can also be a serious sec...

-
Showcasing Incinerator a Powerful Android Malware Reversing Tool
boschko.ca Incinerator: The Ultimate Android Malware Reversing ToolMaster Android malware reversal with ease using Incinerator, your trusted ally in the fight against threat actors for experts and novices alike.

-
Attacking Active Directory Certificate Service Part 2
vandanpathak.com Attacking AD Certificate Services - Part 2I hope you've read the Part-1 of this blog series on basics of AD CS in the environment. In the Part-1 of this blog series, We looked at how we can setup certificate templates or uses the 'User' template to enroll our Windows 7 Minor User with AD CS services. So far we got

-
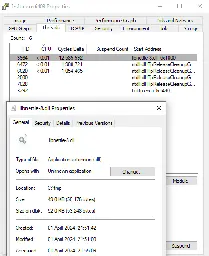
Persistence - DLL Proxy Loading
pentestlab.blog Persistence – DLL Proxy LoadingDLL Proxy Loading is a technique which an arbitrary DLL exports the same functions as the legitimate DLL and forwards the calls to the legitimate DLL in an attempt to not disrupt the execution flow…
-
Adventures in Stegoland - Adventures with a stego shellcode loader
tierzerosecurity.co.nz Tier Zero SecurityInformation Security Services. Offensive Security, Penetration Testing, Mobile and Application, Purple Team, Red Team

- www.oligo.security XZ-actly What You Need (CVE 2024-3094): Detecting Exploitation with Oligo
See how Oligo ADR Detects Exploitation of CVE-2024-3094 (XZ backdoor in liblzma).

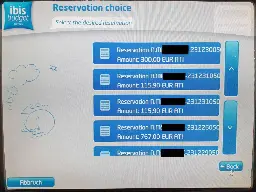
- www.pentagrid.ch IBIS hotel check-in terminal keypad-code leakage
An IBIS hotel check-in terminal leaked room door key codes of almost half of the rooms.
-
NetScout - An OSINT tool I've been working on that finds domains, subdomains, directories and files based on a given URL
github.com GitHub - caio-ishikawa/netscout: OSINT tool that finds domains, subdomains, directories, endpoints and files for a given seed URL.OSINT tool that finds domains, subdomains, directories, endpoints and files for a given seed URL. - caio-ishikawa/netscout
-
Xzbot: exploit demo for the xz backdoor (CVE-2024-3094)
github.com GitHub - amlweems/xzbot: notes, honeypot, and exploit demo for the xz backdoor (CVE-2024-3094)notes, honeypot, and exploit demo for the xz backdoor (CVE-2024-3094) - amlweems/xzbot

- hardenedvault.net xz/liblzma Backdoor: Open Source Nuke? Maybe Not That Bad!
xz/liblzma Backdoor: Open Source Nuke? Maybe Not That Bad! Story Background On March 29, 2024, a report exposing a backdoor in the upstream source code of the controversial open-source project, the xz software package, was made public on the oss-security mailing list.

- remyhax.xyz BGGP4: PleaseMom, QUANTUM, Rat?
For this last years Binary Golf Grand Prix the goal was to: Create the smallest self-replicating file. Requirements: Produce exactly 1 copy of itself Name the copy “4” Not execute the copied file Print, return, or display the number 4 I sat down with some beer, as one does, and resolved that my ...

-
From OneNote to RansomNote: An Ice Cold Intrusion
thedfirreport.com From OneNote to RansomNote: An Ice Cold Intrusion - The DFIR ReportKey Takeaways We provide a range of services, one of which is our Threat Feed, specializing in monitoring Command and Control frameworks like Cobalt Strike, Metasploit, Sliver, Viper, Mythic, Havoc, … Read More

- fidelissecurity.com What is Deception Technology? - Fidelis Security
Discover how deception technology reshapes cyber warfare. Learn how Fidelis Deception enables proactive defense, luring and neutralizing digital adversaries.

- blog.siddarthadukia.com Fine-tuning Semgrep for Ruby Security: Pundit and SQL injection
In this blog post, we’ll go over the construction and tuning of a few Semgrep rules I created while looking at a Ruby on Rails application. Semgrep is a powerful code analysis tool, and while there are a fair number of community rules, the default rules don’t cover everything, and you get a lot more...
-
ROP Emporium - ret2win Buffer Overflow Challenge
vandanpathak.com Return Oriented Programming - ret2win - ROP EmporiumAs i promised, after covering some basics on Return Oriented Programming based Buffer OverFlow, i will continue posting the challenges from ROPEmporium to deep dive in the understanding of ROP based buffer overflow. It took me some time to solve the very first challenge as my environment was giving ...

- blog.gitguardian.com Vulnerability Management Lifecycle in DevSecOps
In this new series, CJ May shares his expertise in implementing secure-by-design software processes that empower engineering teams. The first stage of his DevSecOps program: vulnerability management.

-
Bref Security Audit - Shielder
www.shielder.com Shielder - Bref Security AuditBref Security Audit, sponsored by Amazon Web Services (AWS), facilitated by Open Source Technology Improvement Fund (OSTIF) and performed by Shielder.

- blog.exodusintel.com Mind the Patch Gap: Exploiting an io_uring Vulnerability in Ubuntu - Exodus Intelligence
By Oriol Castejón Overview In early January 2024, a Project Zero issue for a recently fixed io_uring use-after-free (UAF) vulnerability (CVE-2024-0582) was made public. Reading the issue description, it was apparent that the vulnerability allowed an attacker to obtain read and write access to a numb...
-
PyPI Suspends New User Registration In Wake of Large Typosquatting Campaign
blog.phylum.io Typosquatting Campaign Targets Python DevelopersOn 26 March 2024, Phylum’s automated risk detection platform picked up yet another typosquat campaign targeting some attackers’ favorite targets in PyPI. As of writing, this attack still appears to be active and has come in two big waves after about a 20-hour break in between. So far, we’

-
After almost 7 years, new version of drozer was released
github.com GitHub - WithSecureLabs/drozer: The Leading Security Assessment Framework for Android.The Leading Security Assessment Framework for Android. - WithSecureLabs/drozer
- labs.nettitude.com Introducing SharpConflux
Today, we are releasing a new tool called SharpConflux, a .NET application built to facilitate Confluence exploration. It allows Red Team operators to easily investigate Confluence instances with the goal of finding credential material and documentation relating to objectives without having to rely ...
- www.cyberark.com Crumbled Security: Unmasking the Cookie-Stealing Malware Threat
Over the past few years, we’ve seen a huge increase in the adoption of identity security solutions. Since these types of solutions help protect against a whole range of password-guessing and...

-
Malicious Implant to remotely control Electronic Locks via WiFi
blog.pridesec.com.br Turnstiles from a hacker perspective - Part 2Physical implants in turnstiles, replay attacks, and a brief introduction to the Wiegand protocol Disclaimer This Security Advisory is provided on an "as is" basis and do not imply any kind of guarantee or warranty. Your use of the information in this publication or linked materials is at your ow...

-
ANSI Escape sequence injection in wall (util-linux)
github.com GitHub - skyler-ferrante/CVE-2024-28085: WallEscape vulnerability in util-linuxWallEscape vulnerability in util-linux. Contribute to skyler-ferrante/CVE-2024-28085 development by creating an account on GitHub.

