-
Tomb, encrypting your precious data since 2007. Version 2.11 was just released.
github.com Tags · dyne/tombthe Crypto Undertaker. Contribute to dyne/tomb development by creating an account on GitHub.

-
A tool for encrypting files using puzzle based time-lock encryption and password


https://github.com/umutcamliyurt/TimeLockCrypt
- www.newscientist.com Multiple nations enact mysterious export controls on quantum computers
Identical wording placing limits on the export of quantum computers has appeared in regulations across the globe. There doesn't seem to be any scientific reason for the controls, and all can be traced to secret international discussions

cross-posted from: https://sopuli.xyz/post/14485657
> In case of paywall: https://archive.is/kZAgI
-
Javascript cryptography in the wild
github.com GitHub - positive-intentions/chat: Decentralized chatDecentralized chat. Contribute to positive-intentions/chat development by creating an account on GitHub.
in my messaging app, javascript cryptography is the backbone of security so its important for it to be reliable. i would like to introduce you to my decentralized chat app:
https://github.com/positive-intentions/chat
i created thin wrapper around browser-based cryptography functions provided by the browser. it is using webpack 5 module federation to import it at runtime.
https://github.com/positive-intentions/cryptography/blob/staging/src/stories/components/Cryptography.tsx
with this i think i can effectively create encrypted p2p, which i hope to be a step towards true security (but it will take a while to get there).
(note: my app is an experimental unstable proof-of-concept. it is provided for demo and testing purposes.)
-
How to implement a secure Microsoft Recall alternative?
So, I've had a bit of a stupid idea for my next programming project, which would be implementing a Microsoft Recall alternative for Linux where the data is encrypted. I've now written a bit of code and have come to the point where I'd need to encrypt the files. My plan was to use asymmetric encryption where the secret key is again encrypted using something like AES and the user needs to decrypt the private key to view the screenshots taken / data extracted from the screenshots.
I have now learned that asymmetric encryption is very slow and it's generally not designed to encrypt large chunks of data, so I'm not sure how to continue. Do you think asymmetric encryption is feasible for this? Any idea how else to do the encryption? Ideally I would like for the server that takes the screenshots to not have a key that can decrypt the files since that wouldn't be as secure.
- stanfordmag.org Keeping Secrets
Four decades ago, university researchers figured out the key to computer privacy, sparking a battle with the National Security Agency that continues today.

- blog.cryptographyengineering.com A quick post on Chen’s algorithm
If you’re a normal person — that is, a person who doesn’t obsessively follow the latest cryptography news — you probably missed last week’s cryptography bombshell. That news comes…

-
Putty vulnerability: bias in ECDSA deterministic nonce generation leads to compromise of NIST P521 keys with ~60 signatures
writeup from the researcher who discovered this: https://www.openwall.com/lists/oss-security/2024/04/15/6
-
Hatching Secret Sauce Eggs is a Rooster's Business


Hatching Secret Sauce Eggs is a Rooster's Business
This is how I make the secret sauce. The recipe is inside the egg.
- podcasts.google.com Security Cryptography Whatever - Post-Quantum iMessage with Douglas Stebila
Apple iMessage is getting a big upgrade! Not only are they rolling out ratcheting, but they’re going post-quantum, AND they’re doing post-quantum ratcheting! Douglas Stebila joined us to talk about his security analysis of the new PQ3 protocol update and not indulge our wild Apple speculations: Tra...
- arstechnica.com Backdoors that let cops decrypt messages violate human rights, EU court says
Cops have alternative means to access encrypted messages, court says.

- blog.cryptographyengineering.com Attack of the week: Airdrop tracing
It’s been a while since I wrote an “attack of the week” post, and the fault for this is entirely mine. I’ve been much too busy writing boring posts about Schnorr signatures!…

-
28 years later, ETSI's TETRA committee unanimously votes to open source their secret encryption algorithms
www.theregister.com TETRA encryption algorithms entering the public domainEmergency comms standard had five nasty flaws but will be opened to academic research

-
Nearly-finalized eIDAS legislation requires browsers to trust state-issued CAs, and prohibits using certificate transparency to prevent abuses of them: only ETSI-approved authenticity checks allowed.
last-chance-for-eidas.org Last Chance to fix eIDASEU law agreed behind closed doors threatens Internet security
-
Crypto power to the people!

Greetings [email protected]!
At dyne, we're working relentlessly to democratize the power of computing. We've built an open source, multiplatform, tiny, secure, virtual machine for cryptography and blockchain interop. It's called Zenroom. Part of the philosophy behind it is to empower people who know what to do with data, not only the developers and domain experts. To achieve this, it leverages Zencode which allows them to write and review business logic and data-sensitive operations without learning to code. Like this:
But really what it can do is:
- Hashes and signatures (ecdsa, eddsa, Schnorr)
- Quantum-proof crypto (Dilithium, Kyber, NTRU)
- Homomorphic crypto on BLS381
- Interop with Bitcoin and EVM
- Support most widely used curves
- Runs on any platform and in the browser
- No-code programmabiliy using an English-like DSL
We just released v4.0.0 and are always interested in more engaging use cases.
Therefor i'd like to extend you an invitation to a webinar this Friday, November 3rd at 4:30pm UTC+1
You can "signup" here: https://zenroom.org/events/ (basically a calendar .ics)
If you are uncomfortable with Zoom, please know that the video feed will be relayed to our Peertube channel and you will be able to ask questions in the Matrix chat.
Hoping that i'm not breaking any rules of this community and to see you there i send you all warm regards from planet dyne.
edit: removed emoji from title
-
The inability to count correctly: Debunking NIST's calculation of the Kyber-512 security level.
-
https://www.newscientist.com/article/2396510-mathematician-warns-us-spies-may-be-weakening-next-gen-encryption/
-
https://news.ycombinator.com/item?id=37866421
-
https://news.ycombinator.com/item?id=37756656
-
-
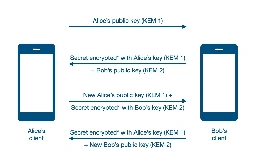
Quantum Resistance and the Signal Protocol
The article is about:
- The Signal Protocol, a set of cryptographic specifications that provides end-to-end encryption for private communications. PQXDH, an upgrade to the Signal Protocol that adds a layer of protection against the threat of a future quantum computer breaking current encryption standards.
- Quantum computing, a new type of computational system that can solve some complex problems faster than classical computers, such as the hidden subgroup problem that underlies many public key cryptosystems4.
- Post-quantum cryptography, a new category of algorithms that resist quantum attacks, and how Signal has chosen CRYSTALS-Kyber as its post-quantum key encapsulation mechanism.
- The implementation and deployment of PQXDH in Signal’s client applications and the open research areas for further quantum resistance.
- scottarc.blog How to Write a Secure JWT Library If You Absolutely Must
I am famously not a fan of JSON Web Tokens (JWT). Like most cryptography and security experts familiar with JWT, I would much rather you use something else if you can. I even proposed a secure alte…

-
AES: How to Design Secure Encryption (Spanning Tree)
cross-posted from: https://lemm.ee/post/5467810
> In 1997, a contest began to develop a new encryption algorithm to become the Advanced Encryption Standard. After years of debate, one algorithm was chosen as the AES. But how does AES work? And what makes for a secure encryption algorithm? > > *** > > Spanning Tree is an educational video series about computer science and mathematics. See more at https://spanningtree.me > > To be notified when a new video is released, sign up for the Spanning Tree mailing list at https://spanningtree.substack.com/ > > Spanning Tree is created by Brian Yu. https://brianyu.me/ > > Email me at [email protected] to suggest a future topic. > > *** > > * 0:00 The Contest > * 1:02 Encryption > * 3:57 Confusion and Diffusion > * 5:44 Block Cipher > * 6:55 KeyExpansion > * 7:34 AddRoundKey > * 8:14 Substitution Cipher > * 8:55 SubBytes > * 11:30 MixColumns > * 12:53 ShiftRows > * 13:21 The Algorithm > > --- > > * https://www.youtube.com/watch?v=C4ATDMIz5wc > * https://piped.video/watch?v=C4ATDMIz5wc > > Aug 22, 2023
- scottarc.blog Innovations in the AWS Database Encryption SDK
In June 2023, Amazon Web Services launched a developer preview of the new Database Encryption SDK in Java for DynamoDB (DB-ESDK for short). The DB-ESDK is the successor to the DynamoDB Encryption C…
-
The Cryptographer Who Ensures We Can Trust Our Computers
www.quantamagazine.org The Cryptographer Who Ensures We Can Trust Our Computers | Quanta MagazineYael Tauman Kalai’s breakthroughs secure our digital world, from cloud computing to our quantum future.

> Yael Tauman Kalai’s breakthroughs secure the digital world, from cloud computing to our quantum future.
> My master’s thesis was titled “How to Leak a Secret.” Here’s the problem: We know how to digitally sign — to say, “This is me that wrote this message.” But say I want to sign something as an MIT professor, but I don’t want people to know it’s me? That way the secret does hold some water because you know an MIT professor signed it, but you don’t know who.
> We solved this with something we called ring signatures, which were inspired by a notion in computer science called witness-indistinguishable proofs. Let’s say there’s a statement and two different ways to prove it. We say there’s two “witnesses” to the statement being correct — each of the proofs. A witness-indistinguishable proof looks the same no matter which you use: It hides which witness you started with.
- zetter.substack.com Interview with the ETSI Standards Organization That Created TETRA "Backdoor"
Brian Murgatroyd spoke with me about why his standards group weakened an encryption algorithm used to secure critical radio communications of police, military, critical infrastructure and others.

-
All cops are broadcasting: breaking TETRA after decades in the shadows
www.midnightblue.nl TETRA:BURST | Midnight BlueTETRA:BURST is a collection of five vulnerabilities, two of which are deemed critical, affecting the Terrestrial Trunked Radio (TETRA) standard used globally by law enforcement, military, critical infrastructure, and industrial asset owners in the power, oil & gas, water, and transport sectors and b...

- yewtu.be 17: Visualizing and Decrypting TLS 1.3 | Learn Wireshark @ SF22US
The title of this class is: "Visualizing and Decrypting TLS 1.3" and was taught by Ross Bagurdes. This was recorded on July 13th in Kansas City, MO. Subscribe to our channel for tons of free Wireshark educational content. To attend a live SharkFest and to learn Wireshark with packet analysis exper...
- yewtu.be Passkeys: The Good, the Bad and the Ugly
Presenter: Christiaan Brand, Product Manager: Security & Identity, Google For years we’ve been told about the imminent arrival of the passwordless future. With the advent of passkey support on Apple, Google and Microsoft platforms, that day has finally arrived. This talk will go into more detail of...
- blog.cryptographyengineering.com On Ashton Kutcher and Secure Multi-Party Computation
Back in March I was fortunate to spend several days visiting Brussels, where I had a chance to attend a panel on “chat control”: the new content scanning regime being considered by the …

- blog.cryptographyengineering.com Book Review: Red Team Blues
As a rule, book reviews are not a thing I usually do. So when I received an out-of-the-blue email from Cory Doctorow last week asking if I would review his latest book, Red Team Blues, it took a mi…
-
an audit of a fintech company's threshold ECDSA implementation yielded four CVEs
research.kudelskisecurity.com Multiple CVEs in threshold cryptography implementationsIntroduction io.finnet hired us to perform a code audit of their threshold ECDSA signature implementation called tss-lib based on the paper UC Non-Interactive, Proactive, Threshold ECDSA with Ident…

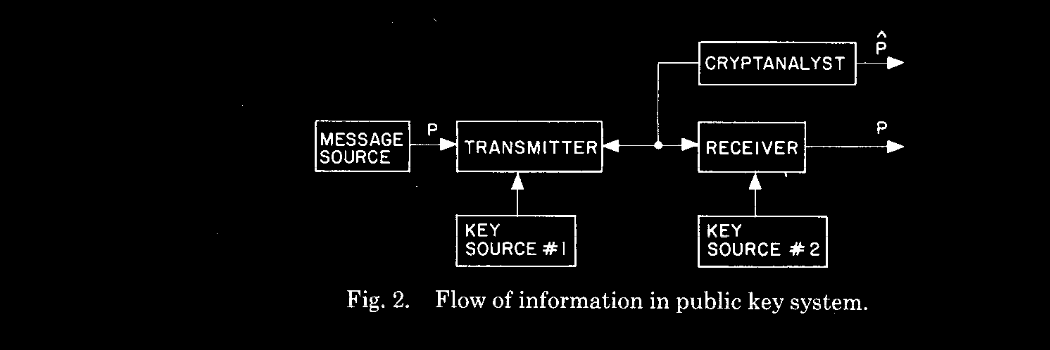
- invidious.projectsegfau.lt Information Security—Before & After Public-Key Cryptography
[Recorded Jan 26, 2005] Whitfield Diffie, a key figure in the discovery of public-key cryptography, traces the growth of information security through the 20th century and into the 21st. In the 1970s, the world of information security was transformed by public-key cryptography, the radical revision o...
- vid.puffyan.us Theory and Practice of Cryptography
Google Tech Talks December, 19 2007 Topics include: Introduction to Modern Cryptography, Using Cryptography in Practice and at Google, Proofs of Security and Security Definitions and A Special Topic in Cryptography This talk is one in a series hosted by Google University: Wednesdays, 11/28/07 - 1...
-
note: this is an updated paper about work that was disclosed last year; I posted a link to the blog of one of the authors to /c/cryptography at the time