-
Privacy/Surveillance Implications of using ISP issued Router?
cross-posted from: https://links.hackliberty.org/post/2005038
I know this is an outrageously bad idea, I don't need convincing. I am just looking for some more information and discussion on what exactly the exposure and surveillance risk is.
I'm asking both for my own education (I am still very green to networking), and to better explain to people in my life if and why they should care.
-
Is it true that traffic can be tracked and logged by ISP through DNS lookups, as these routers are preconfigured to use their internal dns service?
-
If this is changed (like base.dns.mullvad.net), how much does this actually mitigate the risk here?
-
What about when a VPN (mullvad) is also being used at all times? Would it then be "overly paranoid" to fear this untrusted box all the traffic goes through?
I personally take a conservative approach to things like this and assume it's an unacceptable risk, but I don't really understand what the truth is.
Thank you in advance for your time and thoughts.
EDIT: I'm asking about US and US adjacent areas
-
-
[email protected]: An open source two factor auth app that syncs keys between devices?
Isn't the value of two factor auth that it requires a physical device (your phone or computer) with the auth key to authenticate you? Then why don't many two factor auth apps seem to support syncing? If it's fine to do so, are there any open source cross platform apps that sync keys?
- www.theregister.com Police allege ‘evil twin’ in-flight Wi-Fi used to steal info
Fasten your seat belts, secure your tray table, and try not to give away your passwords

- www.cbsnews.com As mind-reading technology improves, Colorado passes first-in-nation law to protect privacy of our thoughts
The first-in-the-nation law in Colorado includes biological or brain data in the State Privacy Act, similar to fingerprints if the data is being used to identify people.

-
Given a perfect weapon, can you commit a perfect crime?
gwern.net <em>Death Note</em>: L, Anonymity & Eluding EntropyApplied Computer Science: On Murder Considered As STEM Field—using information theory to quantify the magnitude of Light Yagami’s mistakes in <em>Death Note</em> and considering fixes

Death Note Anonymity analysis by Gwern.
I think it would be valuable to read for people here, especially newbies and "privacy bros" to understand how
privacy(anonymity) actually works.> Given a perfect weapon, can you commit a perfect crime?
The answer is surprisingly close to no.
> Everything you do bleeds information.
A perfect crime is one that wasn't even noticed. If a perfect crime gets noticed it immediately reveals the following: you are smart and you have the knowledge and weapons to commit a perfect crime, and in a murder you must have had a motive, instantly ruling out 99% of the human population.
On the web you can be tracked using almost anything: browser window size, word choice, times you are online, internet connection delay, negative qualities like not giving your language will exclude the majority of people who do.
In fact, just this post alone is sufficient to narrow me down to less than a million (maybe even a few thousand) people.
Edit: This is actually about anonymity, privacy is slightly different, but I think this is still relevant to privacy.
-
[email protected]: On Simplelogin, are there any practical differences between public and premium domains?
All I found was this comment about the difference.
>Premium domain is only available when you have premium, because fewer people pay and fewer people use it, so there is less abuse and the domain name has better reputation, so when you public domain is not working, using the premium domain may be able to register.
-
[email protected]: What are your thoughts on this old r/Privacy post? 1.6K upvotes "Apple tracks you, even if you don't have Apple devices"
https://reddit.com/r/privacy/comments/v624di/apple\_tracks\_you\_even\_if\_you\_dont\_have\_apple/
>We investigate what data iOS on an iPhone shares with Apple and what data Google Android on a Pixel phone shares with Google. We find that even when minimally configured and the handset is idle both iOS and Google Android share data with Apple/Google on average every 4.5 mins. The phone IMEI, hardware serial number, SIM serial number and IMSI, handset phone number etc are shared with Apple and Google. Both iOS and Google Android transmit telemetry, despite the user explicitly opting out of this. When a SIM is inserted both iOS and Google Android send details to Apple/Google. iOS sends the MAC addresses of nearby devices, e.g. other handsets and the home gateway, to Apple together with their GPS location. Users have no opt out from this and currently there are few, if any, realistic options for preventing this data sharing.
- www.theregister.com Microsoft CEO of AI: Online content is 'freeware' for models
Unless you've got a lawyer, that is

-
[email protected]: Do browsers block websites from uploading data that could be used for fingerprinting like resolution, installed fonts, etc.?
Fingerprinting works by collecting bits of information about the browser and device to identify users. Couldn't browsers see when a website gets such info with JS and either prevent or ask permission from the user for the website to make HTTP requests to upload such information to the website. Idk if they do something like this already.
- www.techradar.com Microsoft has gone too far: including a Game Pass ad in the Settings app ushers in a whole new age of ridiculous over-advertising
Ads in Windows 11 settings are coming next month

-
[email protected]: Are there any privacy issues with keeping camera or mic access on for iOS apps?
iOS is very good about sandboxing and only letting apps run things while the app is open and focused on. It shows green and orange dots when the camera or mic is being used, and none of my use them without saying so and they only do so when they actually need them. If that is the case, are there any potential privacy issues with it?
- www.404media.co Lawsuit Claims Microsoft Tracked Sex Toy Shoppers With 'Recording in Real Time' Software
The complaint claims that Babeland and Good Vibrations websites uses Microsoft's Clarity tracking software to see what visitors searched for and bought.

-
[email protected]: Why use catch-all email domains over email aliases?
I've been looking at using email aliases services, and right now I'm thinking of using Simplelogin for all my online accounts and accounts where I can change my email easily, and getting my own domain to share with people and where I can't easily update my email. It seems like I shouldn't use my own domain for online services because it would be unique and can be tracked.
I did lots of reading about this and am still wondering why someone would want to opt for catch-all domains over aliases. Catch-alls seem highly susceptible to spam and while I haven't actually done any email aliasing yet, it doesn't seem to take much effort to make a new alias if you have a plan with unlimited aliases.
- www.techspot.com Google, Snap, Meta and many others are "quietly" changing privacy policies to allow for AI training
Earlier this year, the Federal Trade Commission warned that companies would be sorely tempted to change the terms and conditions of their privacy statements to allow them...

- arstechnica.com Shopping app Temu is “dangerous malware,” spying on your texts, lawsuit claims
Temu "surprised" by the lawsuit, plans to "vigorously defend" itself.

- arstechnica.com Mac users served info-stealer malware through Google ads
Full-service Poseidon info stealer pushed by "advertiser identity verified by Google."

-
[email protected]: What are the best ways to minimize fingerprinting on Firefox?
I did the tests on fingerprint.com/demo/ and https://coveryourtracks.eff.org/ and they both said I have a unique fingerprint, even when I enabled
privacy.resistFingerprintingtoTrue. -
[email protected]: How well do sites like Blacklight work for checking if sites use trackers?
https://themarkup.org/blacklight, I put in a few sites, including a full Reddit post URL and it reported 0 trackers. Does this site work well, are there other sites for seeing trackers on websites that work well?
- thehackernews.com Google Maps Timeline Data to be Stored Locally on Your Device for Privacy
Starting Dec 1, 2024, Google Maps Timeline data will be stored locally on users' devices, boosting privacy.

"Google has announced plans to store Maps Timeline data locally on users' devices instead of their Google account effective December 1, 2024."
"The development is part of a series of changes the company has enacted in response to allegations that it misled consumers and illegally tracked their movements despite turning off Location History from the account settings by taking advantage of the non-obvious Web & App Activity setting."
-
Is it okay to be cautious about CCTV cameras?


I don't want to sound like a "aluminum foil hat" guy but I'm concerned about CCTV cameras (private and public) around our towns.
All of these cameras do not send the stream to private servers (as the closed circuit would imply) but it's sent to the manufacturers' servers, usually in countries unfriendly to privacy regulations, let alone to human rights. I don't think I'm in immediate danger, but I personally think they likely flow into some AI models and into some government-controlled hands in order to do whatever they want with it.
Another risk is the fact they're very insecure.
I don't know how to battle this. I try not to look directly into a camera when I see one, but that's it. I wish more people would be aware of such risks.
- organicmaps.app The major June update and a follow-up OSM data-only update (with a hotfix for the iOS app hanging) were successfully published and are available in all app stores and on our GitHub.
The major June update and a follow-up OSM data-only update (with a hotfix for the iOS app hanging) were successfully published and are available in all app stor…

- mullvad.net To those of you with nothing to hide: One day you might have. Because you don’t make the rules.
The most common argument used in defense of mass surveillance is ‘If you have nothing to hide, you have nothing to fear’. Try saying that to women in the US states where abortion has suddenly become illegal. Say it to investigative journalists in authoritarian countries. Saying ‘I have nothing to h...

- www.bleepingcomputer.com New Medusa malware variants target Android users in seven countries
The Medusa banking trojan for Android has re-emerged after almost a year of keeping a lower profile in campaigns targeting France, Italy, the United States, Canada, Spain, the United Kingdom, and Turkey.

- www.neowin.net Windows 11 is now automatically enabling OneDrive folder backup without asking permission
Microsoft quietly changed how folder backup works in the OneDrive app on Windows 11. Now, the OS enables it by default during the initial setup without asking the user for permission.

- thehackernews.com Warning: New Adware Campaign Targets Meta Quest App Seekers
Discover how AdsExhaust adware targets Meta Quest app users, manipulates browsers, and generates unauthorized revenue through sophisticated techniques
-
PSA: always update your smartphone | Ratel RAT targets outdated Android phones in ransomware attacks
www.bleepingcomputer.com Ratel RAT targets outdated Android phones in ransomware attacksAn open-source Android malware named 'Ratel RAT' is widely deployed by multiple cybercriminals to attack outdated devices, some aiming to lock them down with a ransomware module that demands payment on Telegram.

- m.youtube.com ‘AI is reliant on mass surveillance’ and we should be cautious, warns head of messaging app | 7.30
Our data is valuable. The information we share online is being used for all sorts of things - to spy on us, influence the advertising we see, train algorithm...

- www.404media.co Hacker Accesses Internal ‘Tile’ Tool That Provides Location Data to Cops
A hacker broke into systems used by Tile, the tracking company, then stole a wealth of customer data and had access to internal company tools.

- www.ghacks.net Microsoft is testing new features in Windows Recall: Screenray and Topics - gHacks Tech News
Microsoft's controversial A.I. tool, Recall, is getting these new features in Windows 11. Here is what you need to know about it.

- www.patrick-breyer.de Chat control vote postponed: Huge success in defense of digital privacy of correspondence!
Today EU governments will not adopt their position on the EU regulation on “combating child sexual abuse”, the so-called chat control regulation, as planned, which would have heralded the end of private messages and secure encryption. The Belgian Council presidency postponed the vote at short notice

Today EU governments will not adopt their position on the EU regulation on “combating child sexual abuse”, the so-called chat control regulation, as planned, which would have heralded the end of private messages and secure encryption. The Belgian Council presidency postponed the vote at short notice. Once again the chat control proposal fails in Council.
- www.theregister.com Signal, MEPs urge EU Council to drop encryption-eroding law
If you call 'client-side scanning' something like 'upload moderation,' it still undermines privacy, security

-
[USA] Appeals court rules that cops can physically make you unlock your phone
reason.com Appeals court rules that cops can physically make you unlock your phoneThe 9th Circuit determined that forcibly mashing a suspect's thumb into his phone to unlock it was akin to fingerprinting him at the police station.
-
How it looks like at the Spyware conference in Prague.
pagenotfound.cz Pronikli jsme na veletrh ISS World Prague. Sponzoruje ho firma pod sankcemi USA – Page Not FoundV tom hotelu je tolik špionážní techniky, že chvílemi při prezentacích kolísá internetové připojení. Do Prahy se opět sjeli na "ples odposlouchávačů" stovky delegátů z celého světa. Novinářům a širší veřejnosti byl tradičně vstup znemožněn. Reportér Page 404 se tam i přes zákaz dostal a mohl se proj...
"They don't let reporters in here!" At an event paid for by a U.S. government blacklisted spy firm. I wonder how many years in a row I'll be able to infiltrate ISS World Prague, since I always post a hilarious photo. (Czech language, can be translated via Deepl)
If you can give @[email protected] subscribe. I just stole it from there.
- proton.me Proton is transitioning towards a non-profit structure | Proton
To ensure our mission always comes first, Proton is transitioning to a non-profit structure and formalizing our promise of people before profits.

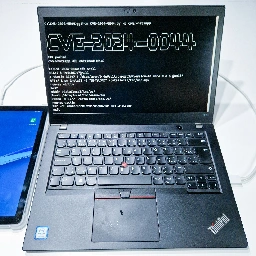
- www.mobile-hacker.com Exfiltrate sensitive user data from apps on Android 12 and 13 using CVE-2024-0044 vulnerability - Mobile Hacker
With physical access to Android device with enabled ADB debugging running Android 12 or 13 before receiving March 2024 security patch, it is possible to access internal data of any user installed app by misusing CVE-2024-0044 vulnerability. Internal data of apps contain sensitive information that ap...
- thehackernews.com Meta Pauses AI Training on EU User Data Amid Privacy Concerns
Meta delays AI training on EU user data following regulatory intervention. Noyb files complaint in 11 European countries alleging GDPR violations.

- www.bleepingcomputer.com Microsoft removes Copilot app ‘incorrectly’ added on Windows PCs
Microsoft says it removed a Copilot app that was "incorrectly" added to Windows 10 and Windows 11 systems in April due to buggy Microsoft Edge updates.

-
Lemmy over Tor Hidden Service (.onion)?
Hello all,
Just wondering if there are any projects involving lemmy and .onion
I searched and didn't see anything but I figured I'd ask
If not is there a reason this isn't possible? Or has nobody cared to do it yet?
When I have to visit r****t I use a libreddit hidden service, and there are quite a few to choose from. Am I correct to think a similar mirror should be about as easy to implement for Lemmy?
an onion only instance where it never touches the clearnet would be really cool too but it would probably be a ghost town (sadly).
Love to hear your thoughts
Thanks
- arstechnica.com Adobe to update vague AI terms after users threaten to cancel subscriptions
Adobe scrambles to earn back user trust by updating terms next week.


